Posts
3498Following
717Followers
1583Marcin Wichary
mwichary@mastodon.onlineI’ve been working on this for a while, but let’s make it official: I started a little Tumblr-like microblog about software craft and quality!
You can sign up via RSS or a weekly newsletter digest. There’s already almost two months of content in there, if you just want to check it out.
Hope you like it!
Gynvael Coldwind 🐈
gynvael@infosec.exchangeJust got this link on my discord - https://www.kickstarter.com/projects/bitman/bootblock-rebels - passing it along because this book looks fun!
small rock formation
algernon@come-from.mad-scientist.clubThe past two months, I've been working on a little pet project, lovingly called OnlyJunk.Fans: hosted iocaine. For free. Because I could, and wanted to.
It's going to officially launch on the 17th of February, in just a few days. But I thought I'll blog about it before the launch, because I won't have time to do so later.
SSD Secure Disclosure
SSDSecureDisclosure@infosec.exchange🚨 New advisory was just published!
Source code review of the Novarain/Tassos framework uncovered 3 critical primitives: unauthenticated file read, unauthenticated file deletion, and SQL injection enabling arbitrary DB reads, affecting 5 widely deployed Joomla! Extensions. Chained together, these bugs allow reliable RCE and administrator account takeover on unpatched Joomla! Instances: https://ssd-disclosure.com/joomla-novarain-tassos-framework-vulnerabilities/
Matthias Kirschner
kirschner@mastodon.social❤️ Thank you to the #Archlinux Wiki maintainers! ❤️
#Maintainers in general, and maintainers of documentation most of the time get way too little recognition for their contributions to #SoftwareFreedom.
ArchWiki is one of the pearls of the internet! That's why I dedicated my this year's #ilovefs post to the #ArchWiki maintainers!
Taggart
mttaggart@infosec.exchangeThe final chapter? The statement from Ars:
On Friday afternoon, Ars Technica published an article containing fabricated quotations generated by an AI tool and attributed to a source who did not say them. That is a serious failure of our standards. Direct quotations must always reflect what a source actually said.
Mr. Bitterness
wdormann@infosec.exchangeArs Technica retracted an article about how AI is making the world worse because...
the Ars article itself contained AI-generated quotes in it.
Welp, we had a decent run, folks. But it's time to call it.
codecolorist
codecolorist@infosec.exchangeNot sure if it’s useful for anyone. 0 dependency parser for plist (xml only) in the browser
buherator
buheratorhttps://github.com/vitoplantamura/BugChecker
r2web now has a built-in code editor 🤟, Edit radare2 scripts right in-browser, Fully mobile UI friendly as always.
watchTowr
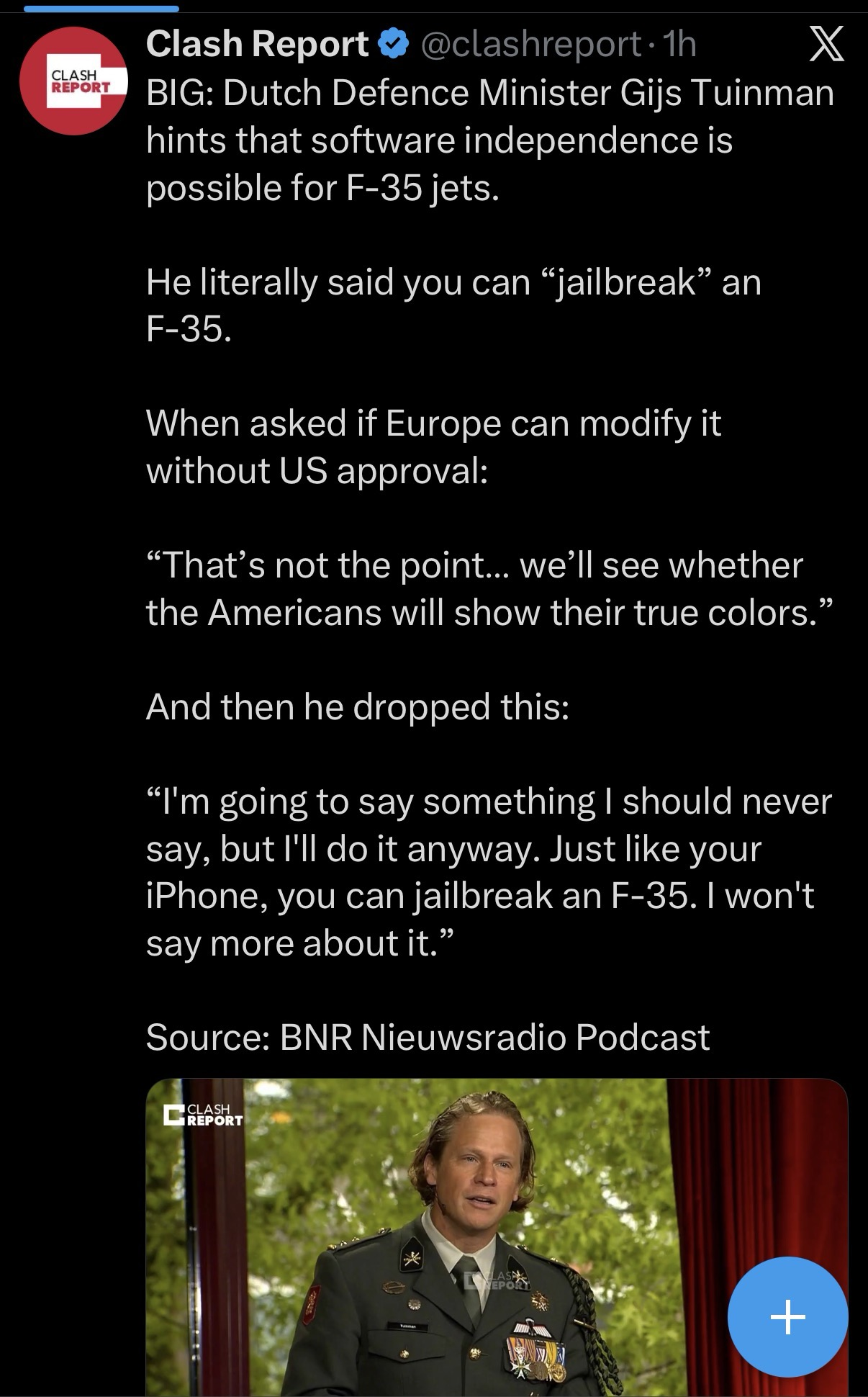
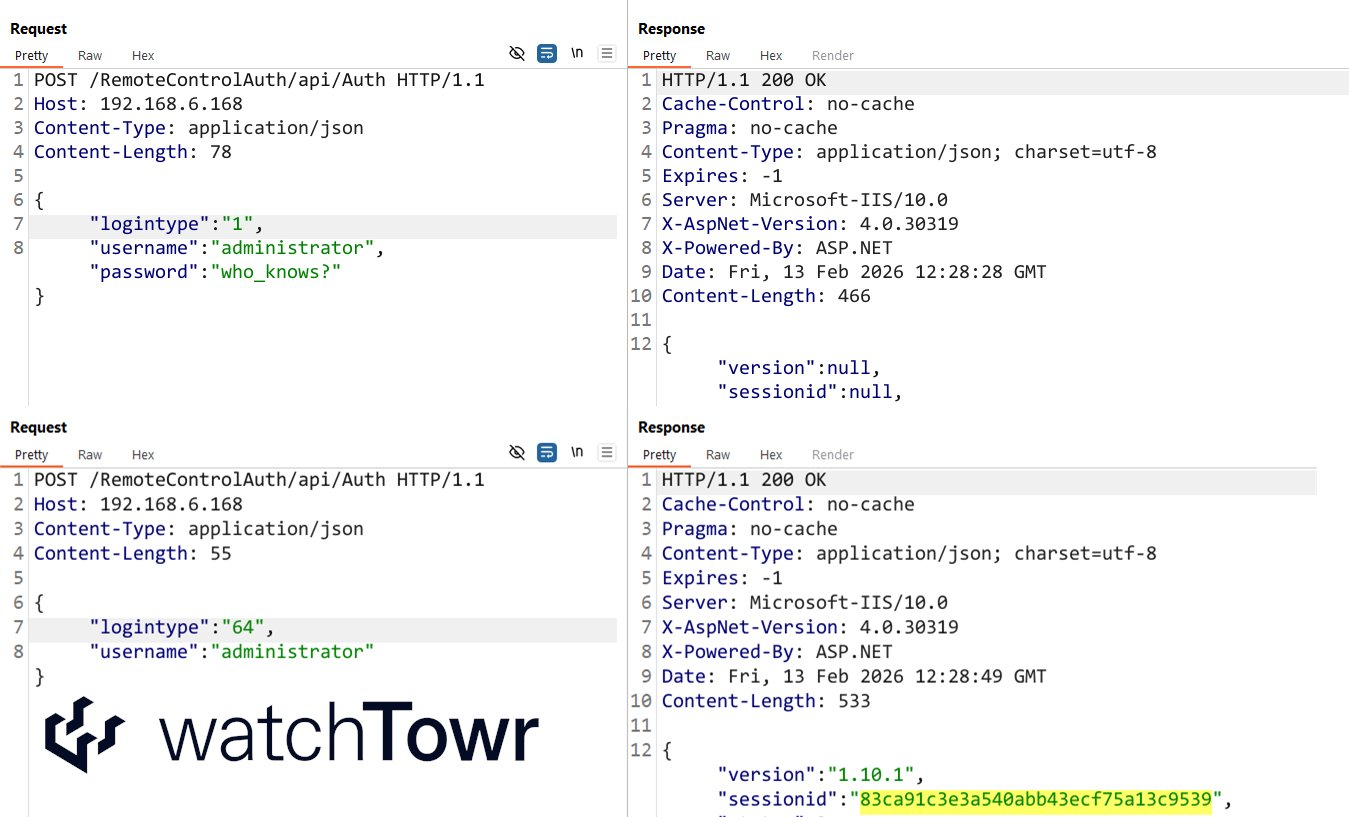
watchTowr@infosec.exchange2026, the year of the AI-driven attacker that could do back flips, they said.
Meanwhile, there's a magic number that allows Auth Bypass against Ivanti EPM (CVE-2026-1603)
something about a pledge 🙄
Frederik Braun �
freddy@security.plumbingNow that we have the infinite monkeys as software, could someone let them know that we don't need someone to write the complete works of Shakespeare again? We have libraries for that.
abadidea
0xabad1dea@infosec.exchangeWhen I said that your discord clone doesn’t need e2ee, I got a lot of comments along the lines of “ then how would I use it to organize the revolution!” The answer is: you don’t. If you have more users than can comfortably share a Signal chat and hence want to use discord or something like it, you cannot POSSIBLY be vetting all of them to a high standard of trust. Your logs ARE leaking. End-to-end encryption between more people than can fit around a dinner table is pointless.
This article confirms what I already assumed, that “open source [information sense, not code sense] intelligence gathering on social media” includes, for the US government, asking for links to join groups that may *feel* private. My own discord has literally like a thousand idlers. It would be very *lucky* if none of them were logging for potentially nefarious purposes! And I remind the active users of this occasionally.
https://www.kenklippenstein.com/p/exclusive-ice-masks-up-in-more-ways
leonjza 
leonjza@infosec.exchange
Had a case this week of a fairly secure deployment of BeyondTrust, but vulnerable to CVE-2026-1731. With basically zero egress, I implemented a timing oracle POC instead. Takes about 20 minutes to get the ls command output in this demo, but hey, it works! :D