Posts
3543Following
722Followers
1584buherator
buheratorWindy city
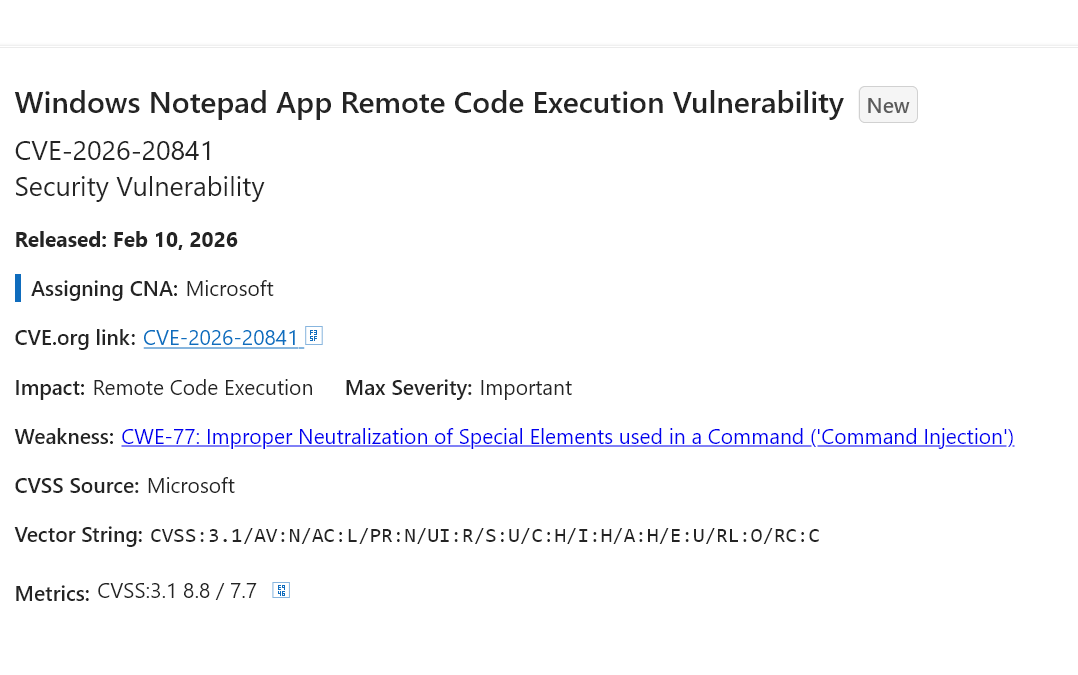
pheonix@hachyderm.ioThey finally did it. Microsoft has successfully over-engineered a text editor into a threat vector.
This CVE is an 8.8 severity RCE in Notepad of all things lmao.
Apparently, the "innovation" of adding markdown support came with the ability of launching unverified protocols that load and execute remote files.
We have reached a point where the simple act of opening a .md file in a native utility can compromise your system. Is nothing safe anymore? 😭
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20841
#noai #microslop #microsoft #windows #programming #writing #windows11 #enshittification #cybersecurity #infosec #technology
0patch
0patch@infosec.exchangeMicropatches released for Windows Telephony Service Elevation of Privilege Vulnerability (CVE-2024-43626)
https://blog.0patch.com/2026/02/micropatches-released-for-windows.html
Infinite Pooh
pooh@mas.to"I'm very glad," said Piglet happily, "that I thought of giving you Something to put in a Useful Pot."
buherator
buheratorhttps://bughunters.google.com/blog/a-joint-security-review-of-intel-tdx-15
buherator
buheratorhttp://blog.quarkslab.com/intego_lpe_macos_1.html
Natasha  🇪🇺
🇪🇺
Natasha_Jay@tech.lgbt
"Switzerland’s military has terminated its contract with Palantir… following a security audit… concluded that U.S. intelligence agencies could potentially access sensitive Swiss defense data… significant reputational warning for the data analytics firm"
https://www.newscase.com/palantirs-swiss-exit-highlights-global-data-sovereignty-challenge/
buherator
buheratorhttps://github.com/NationalSecurityAgency/ghidra/blob/Ghidra_12.0.3_build/Ghidra/Configurations/Public_Release/src/global/docs/ChangeHistory.md
Looks like a fix to a cute little vulnerability too: it seems you could make users execute your commands via @execute annotations in Listings :)
joernchen :cute_dumpster_fire:
joern@threatactor.clubWheeee my presentation on parser differentials made it on the Top Ten Web Hacking Techniques of 2025
https://portswigger.net/research/top-10-web-hacking-techniques-of-2025
buherator
buheratorhttps://access.redhat.com/security/cve/cve-2026-1529
#JWT
iFixit
iFixit@mastodon.socialApple says it supports competition, privacy, and repair. AirPods say “not for you.” From EU feature lockouts to batteries you can’t replace, we unpack Apple’s most disposable design at the link below.
https://www.ifixit.com/News/115572/apple-airpods-and-malicious-compliance
—
#iFixit #RightoRepair #FixTheWorld
buherator
buheratorMe: I don't even know how to type half of these characters :S
AttackerKB
attackerkb"On February 6, 2026, BeyondTrust published an [advisory](https://www.beyondtrust.com/trust-center/security-advisories/bt26-02) for a new critical command injection vulnerability, [CVE-2026-1731](https://nvd.nist.gov/vuln/detail/CVE-2026-1731), affecting their products Remote Support (RS) and Privileged Remote Access (PRA). ..."
Link: https://attackerkb.com/topics/0e038aee-d044-46cf-8b9e-8f54ca24d80a
stf
stf@chaos.socialmy friend @asciimoo built a thing again \o/ and it's great as always. read his own thoughts on this at https://hister.org/posts/how-i-cut-my-google-search-dependence-in-half/
and engage with the cringe on the orange site at https://news.ycombinator.com/item?id=46959554
cirosec GmbH
cirosec@infosec.exchangeThis multi-part blog series is discussing an undocumented feature of Windows: instrumentation callbacks (ICs).
In part 4 we cover ICs from a more theoretical standpoint. Mainly restrictions on unsetting them, how set ICs can be detected and how new ones can be prevented from being set.
Learn more at https://cirosec.de/en/news/windows-instrumentation-callbacks-part-4/