Posts
2987Following
697Followers
1545David Chisnall (*Now with 50% more sarcasm!*)
david_chisnall@infosec.exchangeMitre has just published their top 25 most dangerous software vulnerabilities of 2025
How does #CHERIoT stack up against this list?
5, 7, 8, 11, 14, and 16 are deterministically mitigated with just a recompile.
13 will trap, but is recoverable on a per-compartment basis.
15 is trivial to mitigate with compartmentalisation. Phil Day wrote about this 18 months ago.
6 is mitigated by good capability-based filesystem APIs.
25 is mitigated by our software capability model in the RTOS.
1, 2, 3, 9, 10, 12, 22, and 23 and are not normally applicable on embedded platforms.
That leaves you with a lot more spare brainpower to think about avoiding the remaining seven (4, 17, 18, 19, 20, 21, and 24). The impact of many of these is limited in an environment where there is a programmer model that makes implementing the principles of least privilege and intentional use trivial.
buherator
buheratorhttps://attackanddefense.dev/2025/12/16/attempting-cross-translation-unit-static-analysis.html
buherator
buheratorhttps://www.youtube.com/watch?v=VO4XYoB49Lg
Santa Caws
cR0w@infosec.exchangePublic preview of synced passkeys brings the security benefits of MFA with simpler usability, while avoiding the security risks of weaker MFA options like SMS. However, even the simplest MFA can fail when credentials are lost, making account recovery a critical part of the user experience. To improve usability in such cases, we are introducing public preview for account recovery with AI-powered biometric match against government issued IDs across 192 countries.
buherator
buheratorhttps://blog.thalium.re/posts/dont-judge-an-audiobook-by-its-cover-taking-over-your-amazon-account-with-a-kindle/
buherator
buheratorhttps://github.com/turistu/odds-n-ends/blob/main/CVE-2025-14282.md
buherator
buheratorAlso, Disk Management is gone, and you get no meaningful results for "disk" in the Start Menu. But when you *right click* the Start icon it's there. Why would it be so hard to make this discoverable by search (or leaving a shortcut with the original name)??
Greg K-H
gregkh@social.kernel.orgThat being said, we just assigned our first CVE for some Rust code in the kernel: https://lore.kernel.org/all/2025121614-CVE-2025-68260-558d@gregkh/ where the offending issue just causes a crash, not the ability to take advantage of the memory corruption, a much better thing overall.
Note the other 159 kernel CVEs issued today for fixes in the C portion of the codebase, so as always, everyone should be upgrading to newer kernels to remain secure overall.
Santa Caws
cR0w@infosec.exchangeRE: https://infosec.exchange/@BleepingComputer/115730066370654236
Apparently CVE-2025-59718 and CVE-2025-59719 are now EITW.
buherator
buheratorThe Hacker‘s Choice
thc@infosec.exchange@fwaggle on my Ubuntu 22.0 and 24.0 the ed25519 host public key is not in PEM but in the <type> <key> format (no <comment> section).
What distro uses PEM? I can try to convert it to the type-format and see if the daemon blindly accepts it.
Santa Caws
cR0w@infosec.exchange../ in FreshRSS. How did no one recommend that one to me yesterday? A new ../ would have been fun.
https://github.com/FreshRSS/FreshRSS/security/advisories/GHSA-6c8h-w3j5-j293
Santa Caws
cR0w@infosec.exchangeA couple vulns in Trail of Bits' Fickling.
https://github.com/trailofbits/fickling/security/advisories/GHSA-565g-hwwr-4pp3
https://github.com/trailofbits/fickling/security/advisories/GHSA-r7v6-mfhq-g3m2
Allele Security Intelligence
alleleintel@infosec.exchangeWith H2HC on hiatus this year, the security community stepped up to create the 307 Temporary Security Conference—and we were proud to be part of it!
We presented our research on vulnerabilities in the CAN BCM protocol in the Linux kernel.
Thank you to everyone who watched!
The slides and exploit demos are now available.
Slides
https://allelesecurity.com/wp-content/uploads/2025/12/Presentation_307.pdf
Demo 1: Exploit for UAF read (CAN BCM) to dump shadow file & MySQL root hash.
https://www.youtube.com/watch?v=znTLHc2mXIs
Demo 2: Exploit for UAF read in CAN BCM (CVE-2023-52922) that leaks encoded freelist pointer and slab object addresses
https://www.youtube.com/watch?v=XQ3QlXqn6pI
Trail of Bits
trailofbits@infosec.exchangeMemory bugs, such as use-after-free and buffer overflows, are the most exploited vulnerability class; however, AddressSanitizer's 2-4x performance overhead makes it unusable in production.
So, we recommend GWP-ASan, which uses sampling and guard pages to detect memory safety bugs at scale. Learn the technique and how to implement it in your C++ projects using LLVM's scudo allocator:
https://blog.trailofbits.com/2025/12/16/use-gwp-asan-to-detect-exploits-in-production-environments/
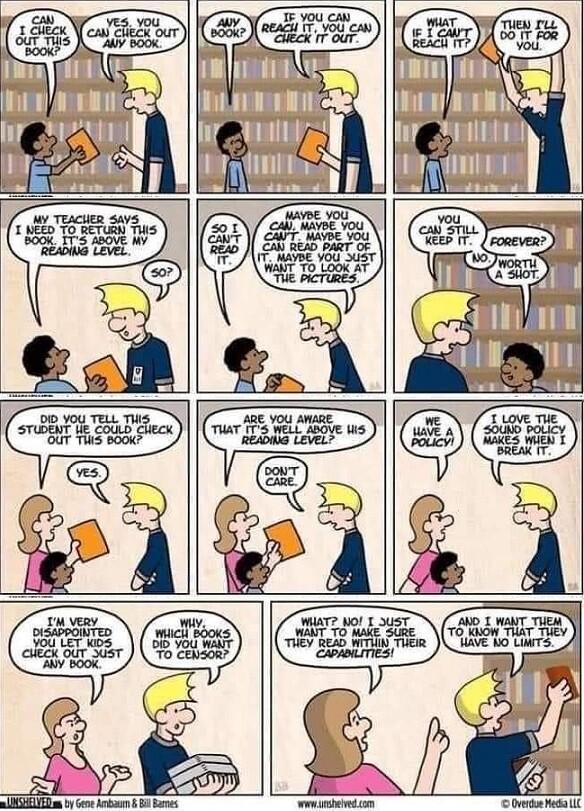
Nick East (Indie Writer)
NickEast_IndieWriter@mastodon.artI want things that are above my reading level, that's how I get better at reading 🤔😁
@reading @bookstodon @books @humor@fedigroups.social @humor@lemmy.world @aiop
#ReadingMemes #Memes
#ReadAllTheBooks #Humor #Humour
#Reading #Readers #ReadersOfMastodon #ReadingCommunity
#Book #Books #Novel #Novels #Fiction
#Bookwyrm #Bookworm #Bookstodon #BookLove #FantasyBooks #ReadingLevel #Level
wirepair
wirepair@mastodon.socialMy second blog post regaling tales from my weekend of bugs: