Posts
2970Following
697Followers
1545Santa Caws
cR0w@infosec.exchangeA couple vulns in Trail of Bits' Fickling.
https://github.com/trailofbits/fickling/security/advisories/GHSA-565g-hwwr-4pp3
https://github.com/trailofbits/fickling/security/advisories/GHSA-r7v6-mfhq-g3m2
Allele Security Intelligence
alleleintel@infosec.exchangeWith H2HC on hiatus this year, the security community stepped up to create the 307 Temporary Security Conference—and we were proud to be part of it!
We presented our research on vulnerabilities in the CAN BCM protocol in the Linux kernel.
Thank you to everyone who watched!
The slides and exploit demos are now available.
Slides
https://allelesecurity.com/wp-content/uploads/2025/12/Presentation_307.pdf
Demo 1: Exploit for UAF read (CAN BCM) to dump shadow file & MySQL root hash.
https://www.youtube.com/watch?v=znTLHc2mXIs
Demo 2: Exploit for UAF read in CAN BCM (CVE-2023-52922) that leaks encoded freelist pointer and slab object addresses
https://www.youtube.com/watch?v=XQ3QlXqn6pI
Trail of Bits
trailofbits@infosec.exchangeMemory bugs, such as use-after-free and buffer overflows, are the most exploited vulnerability class; however, AddressSanitizer's 2-4x performance overhead makes it unusable in production.
So, we recommend GWP-ASan, which uses sampling and guard pages to detect memory safety bugs at scale. Learn the technique and how to implement it in your C++ projects using LLVM's scudo allocator:
https://blog.trailofbits.com/2025/12/16/use-gwp-asan-to-detect-exploits-in-production-environments/
Nick East (Indie Writer)
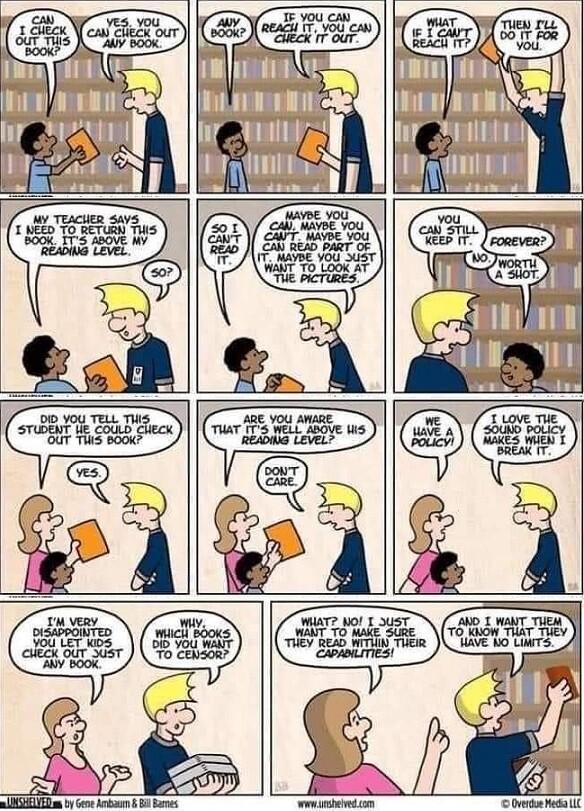
NickEast_IndieWriter@mastodon.artI want things that are above my reading level, that's how I get better at reading 🤔😁
@reading @bookstodon @books @humor@fedigroups.social @humor@lemmy.world @aiop
#ReadingMemes #Memes
#ReadAllTheBooks #Humor #Humour
#Reading #Readers #ReadersOfMastodon #ReadingCommunity
#Book #Books #Novel #Novels #Fiction
#Bookwyrm #Bookworm #Bookstodon #BookLove #FantasyBooks #ReadingLevel #Level
wirepair
wirepair@mastodon.socialMy second blog post regaling tales from my weekend of bugs:
buherator
buheratorYou are dumb and literally everyone hates you.
cryptax
cryptax@mastodon.socialThe Cryptax Award H2 2025 is out! (lol)
Best talks, papers, CTF challenges, tools I encountered in the second half of 2025:
https://cryptax.github.io/nomination-2025-h2/
It's a difficult selection, as always, and it is very personal opinion!
Congratulations to those who are listed, and kudos to others :)
The Hacker‘s Choice
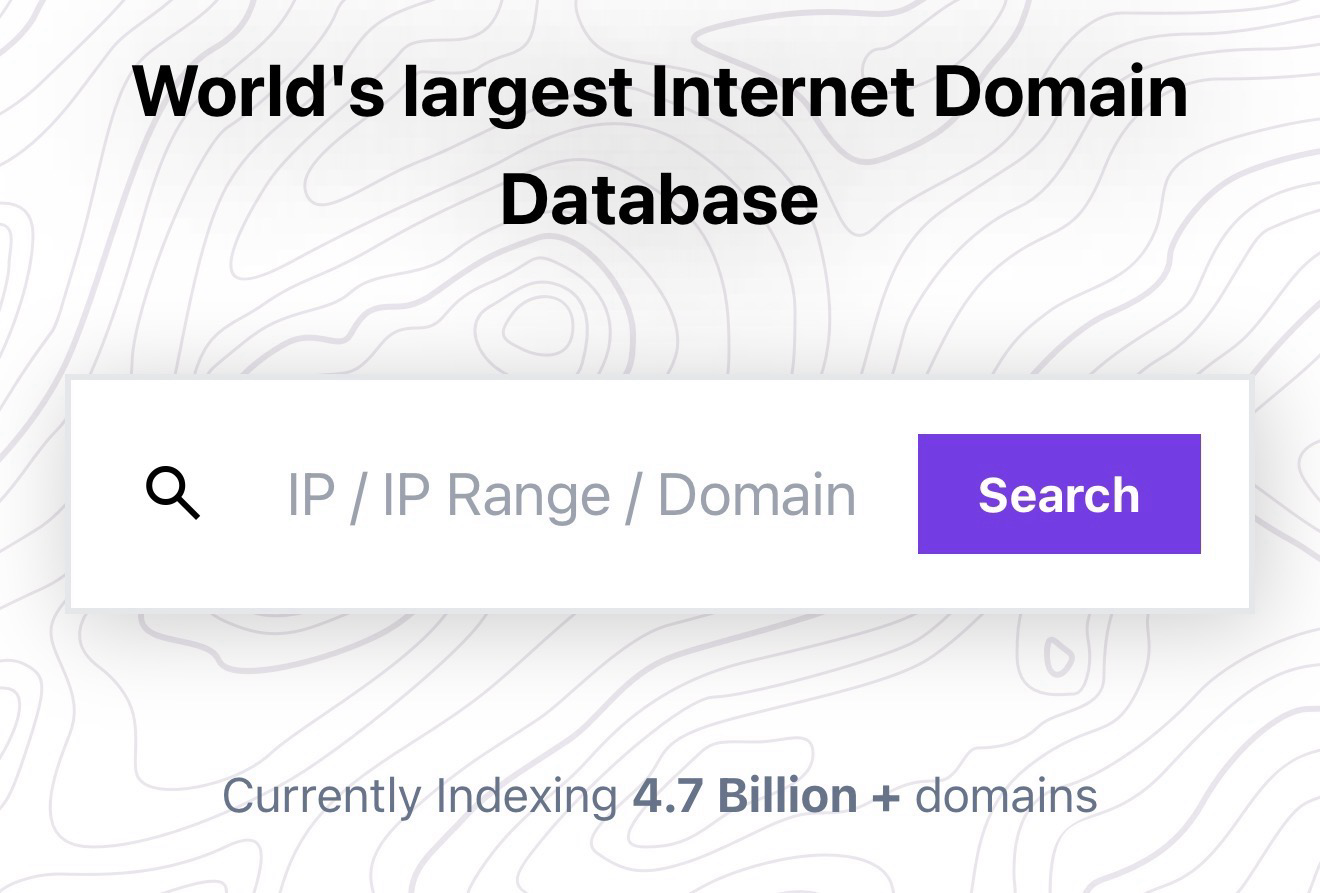
thc@infosec.exchangeTHC Release 💥: The world’s largest IP<>Domain database: https://ip.thc.org
All forward and reverse IPs, all CNAMES and all subdomains of every domain. For free.
Updated monthly.
Try: curl https://ip.thc.org/1.1.1.1
Raw data: https://ip.thc.org/docs/bulk-data-access
(The fine work of messede 👌)
What does everyone think? Need feedback before release tomorrow :)
daniel:// stenberg://
bagder@mastodon.socialIf you need to get your mood down a few notches, there are some new slop entries to torment yourself with here:
https://gist.github.com/bagder/07f7581f6e3d78ef37dfbfc81fd1d1cd
OffensiveCon
offensivecon@mastodon.socialTraining Ticket Shop for #offensivecon26 is now open.
The content of our 2026 trainings is unique and exclusive to OffensiveCon, so don’t miss out.
🔥 New this year: Get your training + conference ticket bundle - you have the opportunity to secure a conference ticket before the conference ticket shop opens!
You can also get a training ticket only...
Training tickets: https://www.offensivecon.org/register.html
And the conference ticket shop? Oh, it’ll open… sometime in the next 5 months. Stay tuned.👀
buherator
buheratordanzin
danzin@mastodon.socialThere's another researcher, Zhengyu Liu, who's been finding CPython crashes (mostly use-after-free) at breakneck speed (19 in 5 days!): https://github.com/python/cpython/issues?q=is%3Aissue%20author%3Ajackfromeast
Not sure about what technique they're using, but their site states they they favor "leveraging program analysis approaches to detect/exploit/patch vulnerabilities in real-world complex applications and systems".
Their reports are comprehensive, with great presentation and details.
danzin
danzin@mastodon.socialThere's a researcher, Jiang Yuancheng, who's doing a great work finding CPython crashes and memory leaks: https://github.com/python/cpython/issues?q=is%3Aissue%20author%3AYuanchengJiang
They've come up with a very clever idea for a new way of fuzzing, made a fine tool out of it, and are reaping great results.
Fuzzing can be a diminishing returns endeavor: you only have so many bugs to find. Their approach has shown itself to cover different areas and kinds of issues well, as shown by their track record.
blacktop
blacktop@mastodon.socialHigh level diff of iOS 26.2 vs. iOS 26.3 beta1 🎉
https://github.com/blacktop/ipsw-diffs/blob/main/26_2_23C55__vs_26_3_23D5089e/README.md