Posts
2850Following
683Followers
1507Remi Gacogne
rgacogne@mamot.frAre other organizations still getting valuable reports on bug bounty programs? Pretty much all of the ones we have received recently at PowerDNS have turned out to be AI lies, to the point I'm seriously considering shutting down our program. Legitimate researchers are almost always contacting us by other means, and I don't want to keep wasting time looking into false, impossible to reproduce reports.
buherator
buherator
pancake 
pancake@infosec.exchange
👀 Before the #radare2 6.0.6 release during the testing stage I spotted a crash on Windows and decided to write a post explaining how I fixed it using only the cmd interface 👉 https://trufae.github.io/aiblog/WinCdbNull-en.html
As a UNIX person I'm not comfortable on #windows but i was happy to learn some commandline #debugging tools and shared some insights for #reverseengineering in my writeup. Hope you enjoy the reading!
Guillotines for a better world
pikesley@mastodon.me.ukSometimes I just get an idea and it won't go away
Edited to add, since this is now doing Numbers:
Fuck the Tories, fuck the Labour party, fuck the TERFs, free Palestine
buherator
buheratorNow that I'm browsing $webapp I realize that modern web is born from the rejection of the constraints implied by the original design: URL's are independent of state, navigation is overridden to oblivion, etc.
Now I truly appreciate hacks that show how you can slip between constraints, but it's not really that: we just removed the constraints entirely and now we wonder why we need an IDE, a transpiler and KB's of CSS to implement <center>.
hermit
alive@interlace.spacehey fedi does anyone know much about reverse engineering fpga bitstreams? is that something that is doable? what tools do people use for this?
looking at a xilinx chip specifically, haven't identified the specific model yet, but it's one that's at least 20 years old
buherator
buheratorhttps://www.synacktiv.com/en/publications/breaking-the-beestation-inside-our-pwn2own-2025-exploit-journey.html
Ooops, I just loaded it in IDA :P Because fuck the software licenses :PPPP
buherator
buheratorJulia Evans
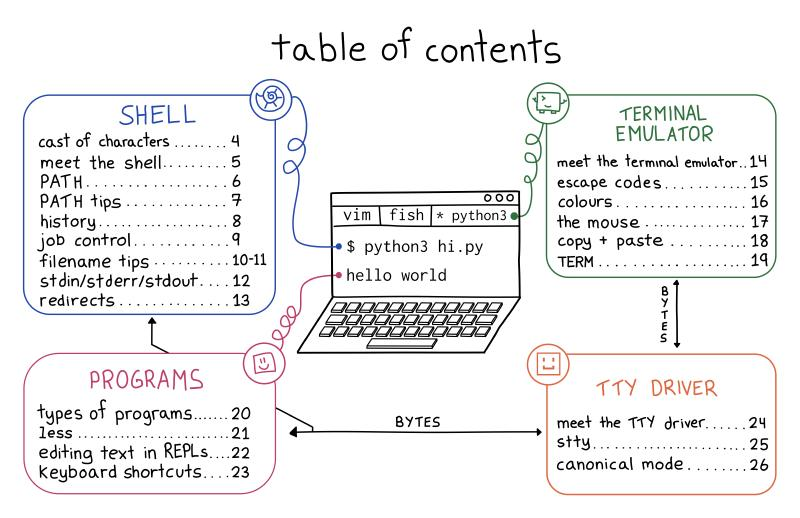
b0rk@jvns.cafirst: my newest zine, The Secret Rules of the Terminal!
This has all the gnarly details about the Unix terminal that I wish I knew when I started using it. It's weird and kind of wonderful (I talk about why you can use your mouse in the terminal!)
https://wizardzines.com/zines/terminal/
(2/16)
Kevin Beaumont
GossiTheDog@cyberplace.socialCellebrite payload dump from a Samsung phone in this thread: https://donotsta.re/objects/482cd0c0-449b-4dbb-8cd4-d63fb86b6334
I’d suggest two things
a) people mirror the download
B) Google and others take a look. From a quick look, it appears they use a zero day in a Linux USB device driver to unlock phone
le epic bacon kira
kirakira@furry.engineerpython, the official language of "well i could just use python"
bitsavers.org
bitsavers@oldbytes.spaceColossal blunder on my part this afternoon.
Pulled the drives from an areca raid array and
forgot what order they have to go back in
so now the array isn't recognized and RESCUE doesn't see it.
Has anyone documented the magic parameter sectors that describe this anywhere?
buherator
buheratorhttps://blog.talosintelligence.com/dell-controlvault-lasso-gl-inet-vulnerabilities/
buherator
buheratorhttps://blog.mantrainfosec.com/blog/18/prepared-statements-prepared-to-be-vulnerable
#nodejs