Posts
2582Following
668Followers
1496
pancake 
pancake@infosec.exchange
“Rowhammer Attacks on DDR5 ::: PTE Exploit Demo” https://www.youtube.com/watch?v=1emxVQ6__qg
buherator
buheratorhttps://aliveteam.github.io/
I'm only now figuring out that today's npm attack is distinct from yesterday's npm attack.
buherator
buheratorI mean, you had one job!
Edit: can't wait for my bank to introduce the "sorry bro, we blew that money on coke" status :D
buherator
buheratorbuherator
buheratorhttps://dirkjanm.io/obtaining-global-admin-in-every-entra-id-tenant-with-actor-tokens/
"I found the most impactful Entra ID vulnerability that I will probably ever find. This vulnerability could have allowed me to compromise every Entra ID tenant in the world"
daniel:// stenberg://
bagder@mastodon.socialWho could have figured out that automatically downloading half the internet and ten thousand always-changing dependencies every time you build could actually be a weakness?
it's missing 🔜 eth0 🎃
domi@donotsta.reTook me way too long due to scope creep, but: The Hacker Webring is now up! 
Members vote for other users. Given enough users, the whole system should work by itself, without administrative intervention.
It’s still somewhat rough around the edges, but functional!
Cure53 🏳️🌈
cure53@infosec.exchangeDOMPurify 3.2.7 has been released today, adding several fixes and improvements.
https://github.com/cure53/DOMPurify/releases/tag/3.2.7
Thanks to all folks who contributed 💕
Julia Evans
b0rk@jvns.caadded a cheat sheet to the official Git website
(with a lot of help from other folks who work on the website)
Yellow Flag
WPalant@infosec.exchangeDrew DeVault writes:
“Perhaps Google and Mozilla, leaders in JavaScript standards and implementations, will start developing a real standard library for JavaScript, which makes micro-dependencies like left-pad a thing of the past.”
There is an interesting logic flaw here. There is in fact String.prototype.padStart built into JavaScript, it has been available for at least eight years. How often did you see that used in production code? Me, having reviewed lots of codebases over the past years – almost never. Meanwhile the cumulative downloads for various string padding libraries on NPM still go into millions per week. It’s not even that many software projects directly depending on them, but way too many projects having complicated dependencies that in some corner of their wide dependency tree aren’t too up to date with these “newfangled” language features.
And if something else is an indicator: I still regularly see jQuery being used in new projects, decades after it became obsolete thanks to browsers improving. No amount of pointing out how harmful it is to sane development patterns helped here.
So I’m not sure that I can see Drew DeVault’s proposed solution to the dependency hell succeeding even if we could get the industry behind it. The inertia behind JavaScript is enormous, and in many areas the usage barely moved beyond JavaScript 1.5. Yet most projects today use a whole array of linters and build tools to aid development, and these are really complicated beasts. Maybe it’s possible to shrink their dependency trees a bit but the complexity isn’t going away.
Maybe the real question is: why does my build process have the potential to compromise my system unless I do some crazy hacks that no sane person would normally bother with? The build result will typically run in some kind of sandbox with very limited damage potential, why doesn’t the build process?
Open Source Security mailing list
oss_security@bird.makeupCVE-2025-6965: SQLite: Integer truncation in findOrCreateAggInfoColumn https://www.openwall.com/lists/oss-security/2025/09/06/1
CVE-2025-7709: SQLite: Integer Overflow in FTS5 Extension https://www.openwall.com/lists/oss-security/2025/09/06/2
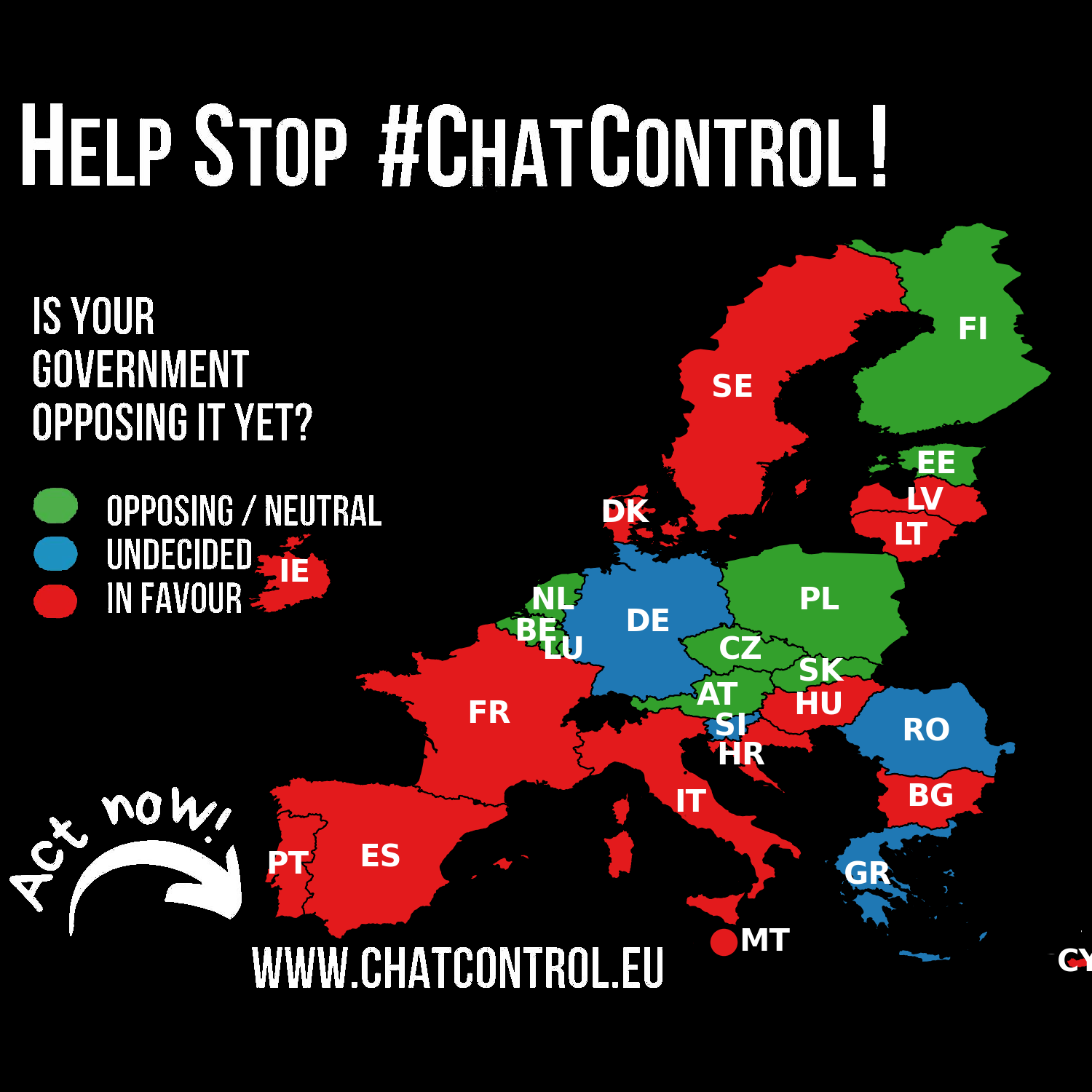
Fight Chat Control
chatcontrol@mastodon.socialGermany's position has been reverted to UNDECIDED.
Despite expressing concerns about breaking end-to-end encryption, Germany refrained from taking a definitive stance on the Chat Control proposal during the September 12th LEWP meeting. A willingness to negotiate and compromise remains.
This is an unfortunate as Germany is crucial to defeating Chat Control.
Please make your voices heard! https://fightchatcontrol.eu/
Source: https://netzpolitik.org/2025/chatkontrolle-noch-haelt-sich-widerstand/
Feoh
feoh@oldbytes.spaceThis is a Dystopian timeline: My wife was let go after 25 years working for the same bank this morning. In an apparent oops, the bank's IT department hard wiped ALL her IOS devices remotely, while she was on the road driving, relying on the GPS function.
The screw you cherry on top? Our apartment building in its infinite wisdom a couple years back switched all building locks to the Latch app.
So she was LOCKED OUT OF OUR HOUSE.
Oh, and the Latch maintained intercom at our front door is out of order.
Thanks for that. Sheesh.
buherator
buheratorhttps://hackaday.com/2025/09/16/2025-hackaday-component-abuse-challenge-let-the-games-begin/
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250916-00/?p=111602
Nothing to see here, move along!
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250916-00/?p=111602
"Nothing to see here!"


 Corveon
Corveon