Posts
2734Following
681Followers
1505GCC Rust
gcc_rust@bird.makeupNew report for the month of May: https://rust-gcc.github.io/2025/06/04/2025-05-monthly-report.html
We are making good progress on core and plan on begin testing the Rust code in the kernel at the end of the summer!
buherator
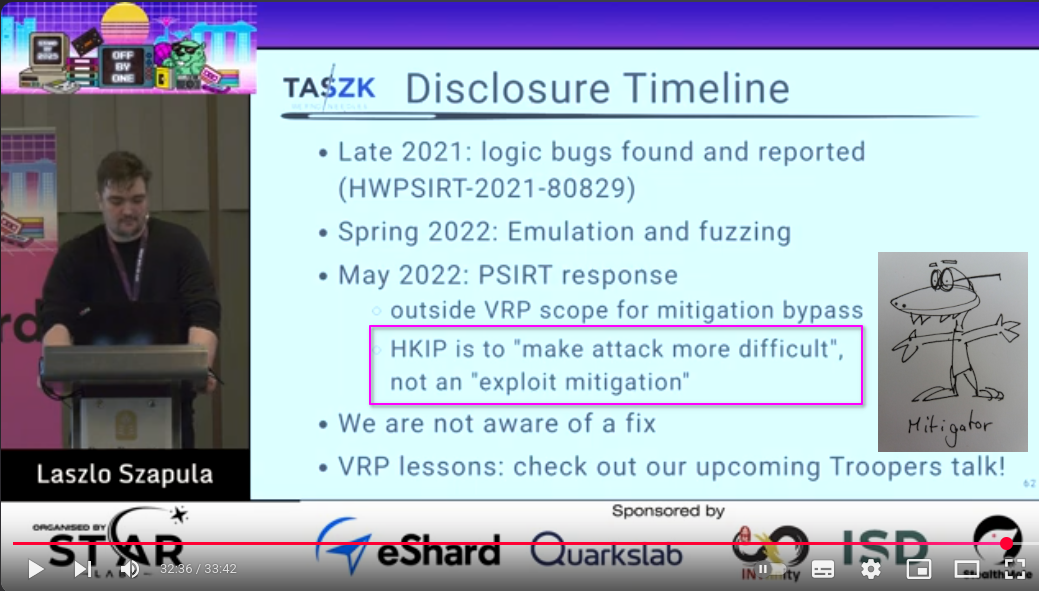
buheratorhttps://www.youtube.com/watch?v=_YtzaU9d-1M
buherator
buheratorhttps://www.linaro.org/blog/introduction-to-kmemdump/
"A smarter way to Capture Crash Data on Embedded Linux Devices"
HN Security
hnsec@infosec.exchangeExploring fault injection on ESP32 V3!
Inspired by Delvaux work, we tested voltage #glitching as an attack vector. With advanced triggers & GDB, we achieved a ~1.5% success rate. #Hardware #FaultInjection is becoming more practical!
https://security.humanativaspa.it/fault-injection-follow-the-white-rabbit/
Robin Adams
robinadams@mathstodon.xyz@inecas @Axolotl1 @davidgerard In Gulliver's Travels, the Laputans had a machine called The Engine that put words together randomly, with scribes writing down any meaningful phrases that happened to be formed.
"Every one knew how laborious the usual method is of attaining to arts and sciences; whereas, by his contrivance, the most ignorant person, at a reasonable charge, and with a little bodily labour, might write books in philosophy, poetry, politics, laws, mathematics, and theology, without the least assistance from genius or study.”
The Wikipedia page for The Engine currently says "See also Large Language Model".
Frédéric Jacobs
fj@mastodon.socialOh WhatsApp, you changed. Meta got the best out of you.
"No one wakes up excited to see more advertising, no one goes to sleep thinking about the ads they'll see tomorrow.”
"Advertising isn't just the disruption of aesthetics, the insults to your intelligence and the interruption of your train of thought.“
~ WhatsApp Blog, June 18th 2012
https://blog.whatsapp.com/why-we-don-t-sell-ads
buherator
buheratorfrycos
frycos@infosec.exchangeA quick-and-dirty late night blog post on discovering an nday variant in Zyxel NWA50AX Pro devices
https://frycos.github.io/vulns4free/2025/06/17/zyxel-nday-variant.html
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/17/4
CVE-2025-6018: LPE from unprivileged to allow_active in *SUSE 15's PAM
CVE-2025-6019: LPE from allow_active to root in libblockdev via udisks
Patrick
pjattke@bird.makeup🚨 New Rowhammer paper 🔨
Our latest work McSee reveals that Intel & AMD CPUs don't use DDR5's RFM cmds 🚫 and Intel uses pTRR on client CPUs 💥
Meet McSee, our oscilloscope-based platform that exposes hidden DDR4/5 behaviors 🧐
Kagi HQ
kagihq@mastodon.socialToday, Kagi celebrates over 50,000 paying subscribers! Check out our latest blog post for exciting updates, including the free Kagi Search portal, Kagi for Libraries, new swag and stickers:
Piotr Bazydło
chudypb@infosec.exchangeMy Sitecore CMS pre-auth RCE chain blog is public now. Enjoy 🫡
https://labs.watchtowr.com/is-b-for-backdoor-pre-auth-rce-chain-in-sitecore-experience-platform
Piotr Bazydło
chudypb@infosec.exchangeRecording of my Hexacon talk "Exploiting Hardened .NET Deserialization: New Exploitation Ideas and Abuse of Insecure Serialization" is available!
Talk: https://youtu.be/_CJmUh0_uOM?si=81Tot7HUgp7RQAlL
White paper: https://github.com/thezdi/presentations/blob/main/2023_Hexacon/whitepaper-net-deser.pdf
I hope you will find it useful :)
Piotr Bazydło
chudypb@infosec.exchangeAnd domain-level RCE in Veeam B&R fixed today (CVE-2025-23121). My first (and hopefully not last) CVE, where I'm credited together with @codewhitesec 😎
in case you missed it, someone has been porting mario64 to the gameboy advance
in what i can only describe as incredible hackery
https://www.youtube.com/watch?v=kueoO3b4B-M
technically speaking, it isn't the first 3d game on the gba, there's games like "asterix and obelix xxl"
technically speaking though, porting an n64 game to the gba is even more ridiculous
Linux Kernel Security
linkersec@bird.makeupThe researchers leaked the kernel base address using the EntryBleed side-channel attack and then turned the UAF on the vsock_sock structure into a RIP control primitive to execute a ROP-chain.