Posts
2524Following
646Followers
1460Kagi HQ
kagihq@mastodon.socialToday, Kagi celebrates over 50,000 paying subscribers! Check out our latest blog post for exciting updates, including the free Kagi Search portal, Kagi for Libraries, new swag and stickers:
Piotr Bazydło
chudypb@infosec.exchangeMy Sitecore CMS pre-auth RCE chain blog is public now. Enjoy 🫡
https://labs.watchtowr.com/is-b-for-backdoor-pre-auth-rce-chain-in-sitecore-experience-platform
Piotr Bazydło
chudypb@infosec.exchangeRecording of my Hexacon talk "Exploiting Hardened .NET Deserialization: New Exploitation Ideas and Abuse of Insecure Serialization" is available!
Talk: https://youtu.be/_CJmUh0_uOM?si=81Tot7HUgp7RQAlL
White paper: https://github.com/thezdi/presentations/blob/main/2023_Hexacon/whitepaper-net-deser.pdf
I hope you will find it useful :)
Piotr Bazydło
chudypb@infosec.exchangeAnd domain-level RCE in Veeam B&R fixed today (CVE-2025-23121). My first (and hopefully not last) CVE, where I'm credited together with @codewhitesec 😎
in case you missed it, someone has been porting mario64 to the gameboy advance
in what i can only describe as incredible hackery
https://www.youtube.com/watch?v=kueoO3b4B-M
technically speaking, it isn't the first 3d game on the gba, there's games like "asterix and obelix xxl"
technically speaking though, porting an n64 game to the gba is even more ridiculous
Linux Kernel Security
linkersec@bird.makeupThe researchers leaked the kernel base address using the EntryBleed side-channel attack and then turned the UAF on the vsock_sock structure into a RIP control primitive to execute a ROP-chain.
Linux Kernel Security
linkersec@bird.makeupExploiting the CVE-2025-21756 1-day vulnerability
@v4bel and @_qwerty_po posted a kernelCTF report about exploiting a UAF in the vsock subsystem of the Linux kernel:
https://github.com/google/security-research/blob/f7dbb569a8275d4352fb1a2fe869f1afa79d4c28/pocs/linux/kernelctf/CVE-2025-21756_lts_cos/docs/exploit.md
Another sev:CRIT ../ ? This time in ZendTo. LMAO. PoC in the post.
We discovered a path traversal vulnerability in ZendTo versions 6.15-7 and prior. This vulnerability allows malicious actors to bypass the security controls of the service to access or modify potentially sensitive information of other users. This issue is patched in 6.15-8, and we encourage all users to upgrade as soon as possible.
buherator
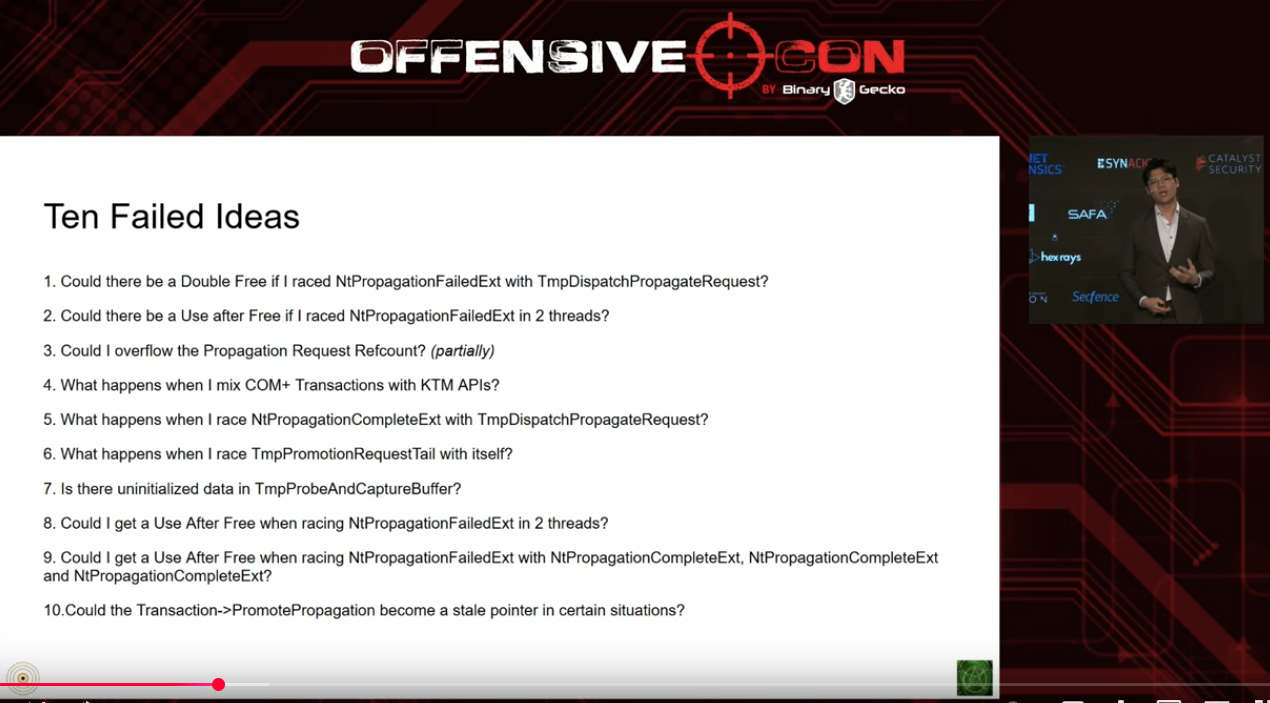
buheratorhttps://www.youtube.com/watch?v=goEb7eKj660
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/17/1
Insinuator
Insinuator@infosec.exchangeNew post: Disclosure: Multiple Vulnerabilities in X.Org X server prior to 21.1.17 and Xwayland prior to 24.1.7 https://insinuator.net/2025/06/disclosure-multiple-vulnerabilities-xserver-xwayland/
Doyensec
doyensec@infosec.exchange🚀 We have just released a new Security Advisory for NASA's CFITSIO library 🛰️. Click the link for details on the Heap Overflow, Type Confusion, Out-of-Bound Writes & other vulnerabilities discovered by our Adrian Denkiewicz !
https://www.doyensec.com/resources/Doyensec_Advisory_CFITSIO_Q22025.pdf
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/16/6
CVE-2025-49794 CVE-2025-49795 CVE-2025-49796 CVE-2025-6021 CVE-2025-6170
CVE-2025-6021 looks like the most severe (integer overflow in xmlBuildQName())
buherator
buheratorhttps://www.youtube.com/playlist?list=PLiIDIO1Gp6V9t5jA1WnTVAfHNPPR9OhSx
https://www.youtube.com/playlist?list=PLiIDIO1Gp6V8_CMvMVabhyeABTW1yZrRZ
buherator
buheratorhttps://r0keb.github.io/posts/Junk-Code-Engines-for-Polymorphic-Malware/