Posts
3373Following
712Followers
1579Another sev:CRIT ../ ? This time in ZendTo. LMAO. PoC in the post.
We discovered a path traversal vulnerability in ZendTo versions 6.15-7 and prior. This vulnerability allows malicious actors to bypass the security controls of the service to access or modify potentially sensitive information of other users. This issue is patched in 6.15-8, and we encourage all users to upgrade as soon as possible.
buherator
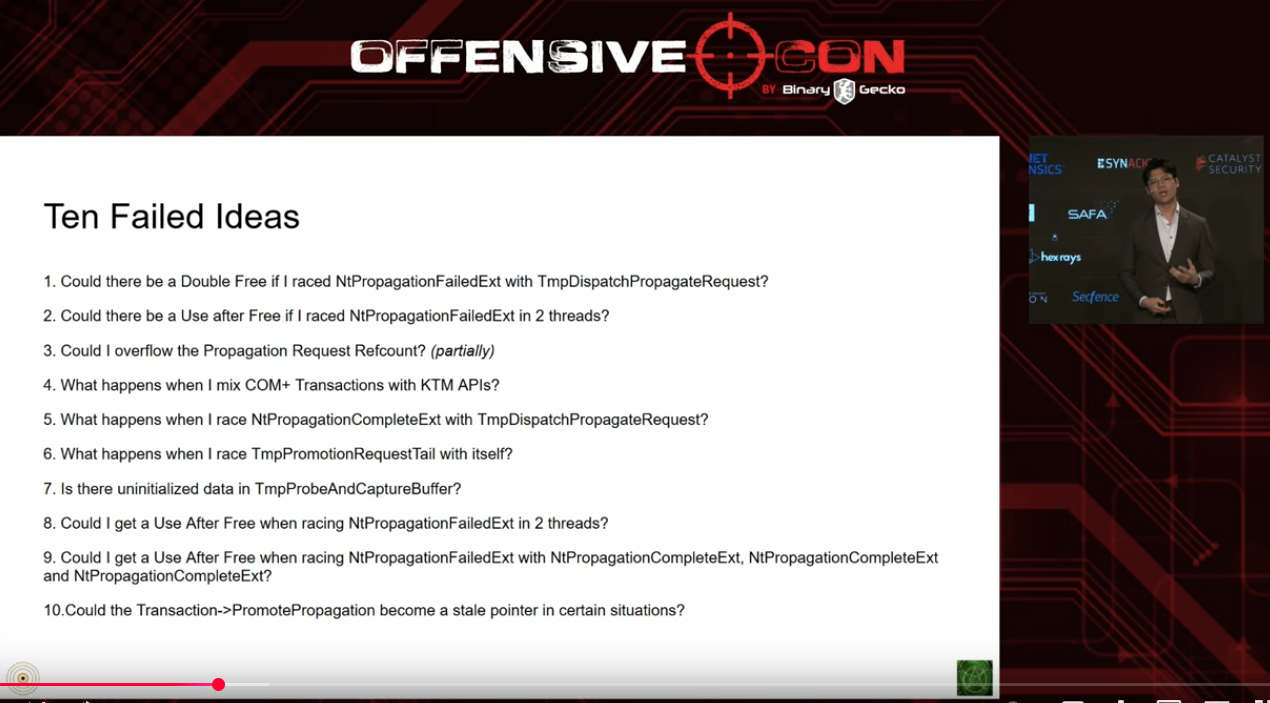
buheratorhttps://www.youtube.com/watch?v=goEb7eKj660
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/17/1
Insinuator
Insinuator@infosec.exchangeNew post: Disclosure: Multiple Vulnerabilities in X.Org X server prior to 21.1.17 and Xwayland prior to 24.1.7 https://insinuator.net/2025/06/disclosure-multiple-vulnerabilities-xserver-xwayland/
Doyensec
doyensec@infosec.exchange🚀 We have just released a new Security Advisory for NASA's CFITSIO library 🛰️. Click the link for details on the Heap Overflow, Type Confusion, Out-of-Bound Writes & other vulnerabilities discovered by our Adrian Denkiewicz !
https://www.doyensec.com/resources/Doyensec_Advisory_CFITSIO_Q22025.pdf
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/16/6
CVE-2025-49794 CVE-2025-49795 CVE-2025-49796 CVE-2025-6021 CVE-2025-6170
CVE-2025-6021 looks like the most severe (integer overflow in xmlBuildQName())
buherator
buheratorhttps://www.youtube.com/playlist?list=PLiIDIO1Gp6V9t5jA1WnTVAfHNPPR9OhSx
https://www.youtube.com/playlist?list=PLiIDIO1Gp6V8_CMvMVabhyeABTW1yZrRZ
buherator
buheratorhttps://r0keb.github.io/posts/Junk-Code-Engines-for-Polymorphic-Malware/
Julia Evans
b0rk@jvns.cathis is a nice post on strace (I didn't know that strace had a --stack-traces option!) https://rrampage.github.io/2025/06/13/strace-tips-for-better-debugging/
buherator
buheratorhttps://github.com/v-p-b/prefetch-lib
For dogfooding I exploited HEVD on Windows 11 24H2:
https://github.com/v-p-b/HEVD-prefetch
buherator
buheratorhttps://www.openwall.com/lists/oss-security/2025/06/16/5
Exquisite bug!
0patch
0patch@infosec.exchangeThis exploited-in-the-wild issue is an interesting twist on binary planting that we were working on a decade and a half ago. The DLL/EXE search order just keeps on giving (to attackers, that is). https://binaryplanting.com
It turned out that all our security-adopted Windows versions were affected by this issue, so we created micropatches for them all. These are already distributed and applied to all online affected systems.
We would like to thank security researchers Alexandra Gofman and David Driker with @_cpresearch_ for detecting the exploitation and publishing their analysis, which made it possible for us to create a micropatch for this issue.
0patch
0patch@infosec.exchangeMicropatches Released for WEBDAV Remote Code Execution Vulnerability (CVE-2025-33053) https://blog.0patch.com/2025/06/micropatches-released-for-webdav-remote.html