Posts
3373Following
712Followers
1579buherator
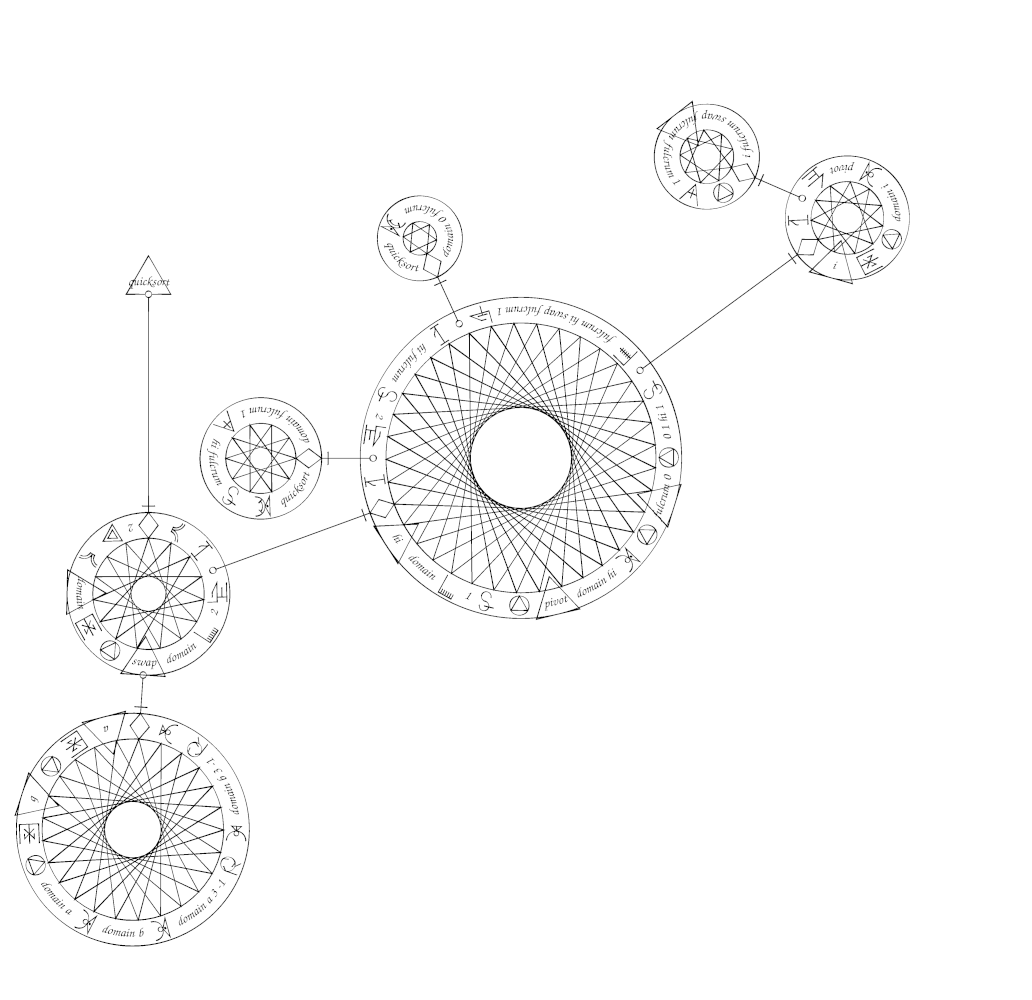
buheratorhttps://suberic.net/~dmm/projects/mystical/README.html
h/t @neauoire
Devine Lu Linvega
neauoire@merveilles.townA programming language that resembled magical circles.
docs: https://suberic.net/~dmm/projects/mystical/README.html
All sigils: https://suberic.net/~dmm/projects/mystical/docs/operators.html
by @yomikoma
Lorin Hochstein 
norootcause@hachyderm.io
Them: The real threat to reliability is all this complexity in our system!
Me: Wait, so those corrective actions that you proposed in the wake of that last incident, would they *reduce* complexity or *increase* it?
Them: …
Me: …
TrendAI Zero Day Initiative
thezdi@infosec.exchangePwn2Own Berlin 2025 comes to a close. We awarded $1,078,750 for 28 unique 0-days. Congrats to STAR Labs SG for winning Master of Pwn with $320,000. Thanks to @offensive_con for hosting, and thanks to all who participated. Can't wait to see you next year! #Pwn2Own #P2OBerlin
Open Source Security mailing list
oss_security@bird.makeupGLIBC-SA-2025-0002: CVE-2025-4802: glibc: elf: static setuid binary dlopen may incorrectly search LD_LIBRARY_PATH https://www.openwall.com/lists/oss-security/2025/05/17/2
Affects statically linked setuid binaries that call dlopen, including internally to glibc after setlocale or NSS functions such as getaddrinfo
buherator
buheratorhttps://cyberscoop.com/coinbase-cyberattack-extortion-counter-reward/
buherator
buheratorhttps://labs.watchtowr.com/expression-payloads-meet-mayhem-cve-2025-4427-and-cve-2025-4428/
buherator
buheratorhttps://github.com/google/security-research/security/advisories/GHSA-qx2m-rcpc-v43v
buherator
buheratorAchievement unlocked: featured in exploits.club newsletter \o/
https://blog.exploits.club/exploits-club-weekly-newsletter-72-windows-on-windows-coreaudio-fuzzing-virtualbox-escapes-and-more/
TrendAI Zero Day Initiative
thezdi@infosec.exchangeWrapping up Day Two of #Pwn2Own Berlin 2025. We’ve awarded $695,000 for 20 unique 0-days, with one more day to go!
Jan Wildeboer 😷
jwildeboer@social.wildeboer.net
Dear #Letsencrypt, you helped secure millions and millions of servers, not just web servers. But your announcement at https://letsencrypt.org/2025/05/14/ending-tls-client-authentication/ about ending Ending TLS Client Authentication Certificate Support in 2026 because Google changes their requirements would result in your certificates being unusable for SMTP servers. You are literally risking an email collapse for many mailserver owners just to please Google? Please think again. Please.
joernchen :cute_dumpster_fire:
joern@threatactor.clubTrendAI Zero Day Initiative
thezdi@infosec.exchangeConfirmed!! Dinh Ho Anh Khoa of Viettel Cyber Security combined an auth bypass and an insecure deserialization bug to exploit #Microsoft SharePoint. He earns $100,000 and 10 Master of Pwn points. #Pwn2Own #P2OBerlin
Peter Schaar
PWS_1@mastodon.social#Microsoft has blocked its services to the International Criminal Court by order of Donald #Trump. The #ICC prosecutor doesn’t have access to his #email. Source:AP
https://apnews.com/article/icc-trump-sanctions-karim-khan-court-a4b4c02751ab84c09718b1b95cbd5db3
Virus Bulletin
VirusBulletin@infosec.exchangeG DATA's Karsten Hahn details how software downloads for the printer company Procolored were infected with XRed backdoor for half a year. https://www.gdatasoftware.com/blog/2025/05/38200-printer-infected-software-downloads
Dr. Christopher Kunz
christopherkunz@chaos.socialCISA is changing the way they publizice alerts, including the KEV (known exploited vulnerabilities). These will no longer be shown on the "Alerts" overview, but must be subscribed to via GovAlert (or just scrape the JSON...).
The first vulnerability that is *not* being published as an alert is...drumroll... CVE-2025-47729. "The TeleMessage archiving backend through 2025-05-05 holds cleartext copies of messages from TM SGNL app users"
Isn't that a funny coincidence?
Jan Wildeboer 😷
jwildeboer@social.wildeboer.net
I am totally sure (sarcasm included) that #Google has totally overseen that their planned changes to their root program requirements will cause a lot of problems for mailserver owners like me who in future might run into weird problems with #Letsencrypt certificates for SMTP. I am sure that Google is absolutely not trying to make running your own mailserver even more complicated just to protect their gmail business. That would be totally not how Google thinks, amirite? https://letsencrypt.org/2025/05/14/ending-tls-client-authentication/
daniel:// stenberg://
bagder@mastodon.socialDetecting malicious Unicode in #curl
https://daniel.haxx.se/blog/2025/05/16/detecting-malicious-unicode/
Sam Stepanyan  🐘
🐘
securestep9@infosec.exchange
CISA Warns of #Google Chromium #ZeroDay Vulnerability CVE-2025-4664 Actively Exploited in the Wild affecting #Chrome, MS #Edge and Opera – Make sure to update your browser to the latest version today!
👇
https://cybersecuritynews.com/cisa-warns-of-google-chromium-vulnerability-actively-exploited-in-the-wild/
那个火饺🦆(JJ)
thatjiaozi@bird.makeupI wanted to end last year with a vm escape, took me a bit longer but I want to present you my latest public research:
A VM escape in Oracle VirtualBox using only one integer overflow bug!
This was fixed in April 15 and assigned CVE-2025-30712.
https://github.com/google/security-research/security/advisories/GHSA-qx2m-rcpc-v43v