Posts
2437Following
590Followers
1307Heretek of Silent Signal
Not a Goat 🦝
screaminggoat@infosec.exchangeOracle: Oracle Critical Patch Update Advisory - January 2025
It's a pain in the butt to read, but there's 300+ vulnerabilities and coupled with the Oracle VP of Security Assurance's blog post January 2025 Critical Patch Update Released, there's likely no mention of exploitation.
See related The Hacker News reporting: Oracle Releases January 2025 Patch to Address 318 Flaws Across Major Products
#oracle #vulnerability #PatchTuesday #cve #infosec #cybersecurity
Ange
Ange@mastodon.socialWhat I call file format hexploring:
Read the specs, read parsers, craft pocs by hand if possible, explore the history and the features timeline, understand abuses, analyse at a low level…
Techmeme
Techmeme@techhub.socialThe Trump administration removed all advisory committee members within the DHS, including those in CISA and CSRB, which was investigating Salt Typhoon (Becky Bracken/Dark Reading)
https://www.darkreading.com/threat-intelligence/trump-fires-cyber-safety-board-salt-typhoon-hackers
http://www.techmeme.com/250122/p3#a250122p3
Zero Day Initiative
thezdi@infosec.exchangeWell that's awkward. @EQSTLab used a OS command injection bug, but it was one used last year. Alpine chose not to patch it since "in accordance with ISO21434...the vulnerability is classified as 'Sharing the Risk'." Yikes. The @EQSTLab team earns $5,000 and 1 Master of Pwn point.
hackaday
hackaday@hackaday.socialGoing Minimal: 64×4, The Fun in Functional Computing
https://hackaday.com/2025/01/22/going-minimal-64x4-the-fun-in-functional-computing/
Andy Greenberg
agreenberg@infosec.exchangeTrump pardons Ross Ulbricht after eleven years in prison. An incredible twist in the never-ending Silk Road saga.
https://www.wired.com/story/trump-frees-silk-road-creator-ross-ulbricht-after-11-years-in-prison/
Michał "rysiek" Woźniak · 🇺🇦
rysiek@mstdn.socialThere's a "Signal deanonymized" thing going around:
https://gist.github.com/hackermondev/45a3cdfa52246f1d1201c1e8cdef6117
Stay calm. Deep breaths.
👉 while this is a real consideration, the only thing the attacker gets from this is a very rough (kilometers or tens of kilometers radius) location
👉 other communication platforms that use any kind of caching CDN to deliver attachments are just as vulnerable
👉 you almost certainly should continue to use Signal, unless you specifically know that this is a big problem for you.
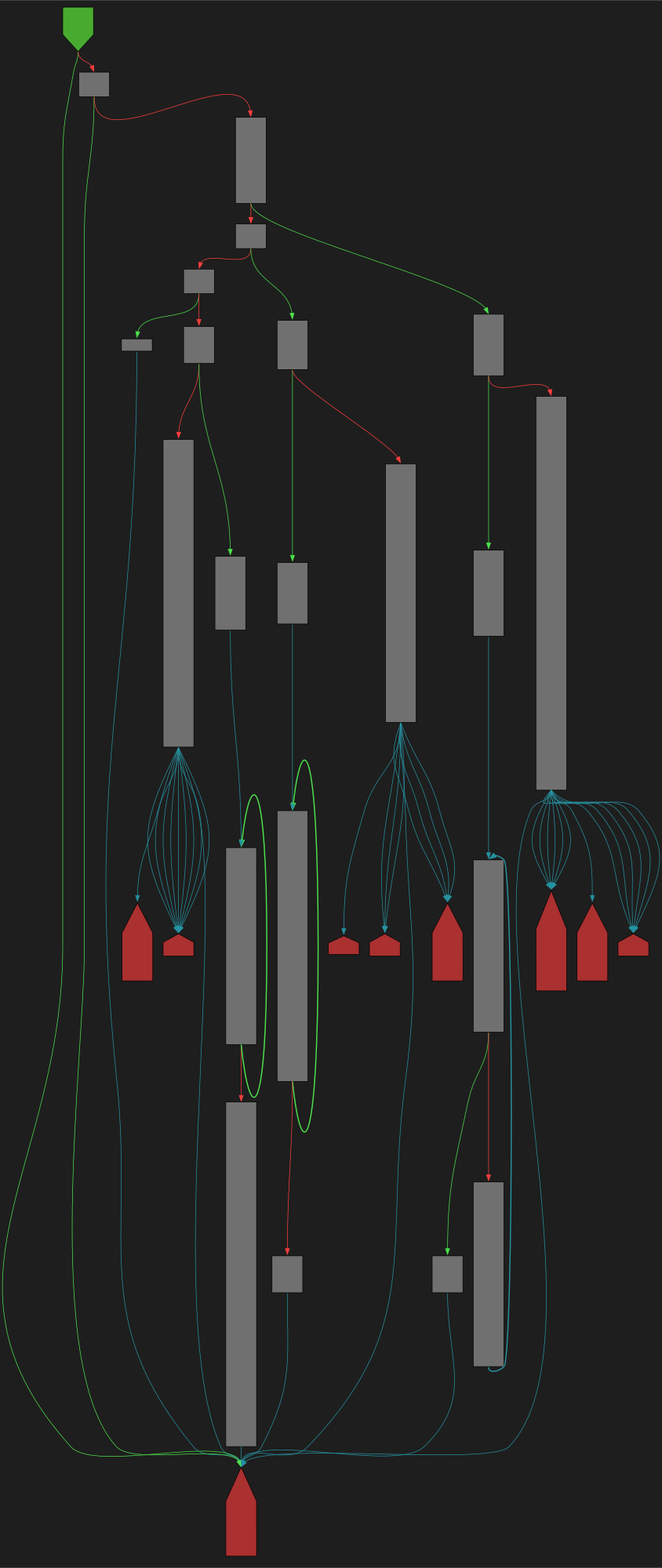
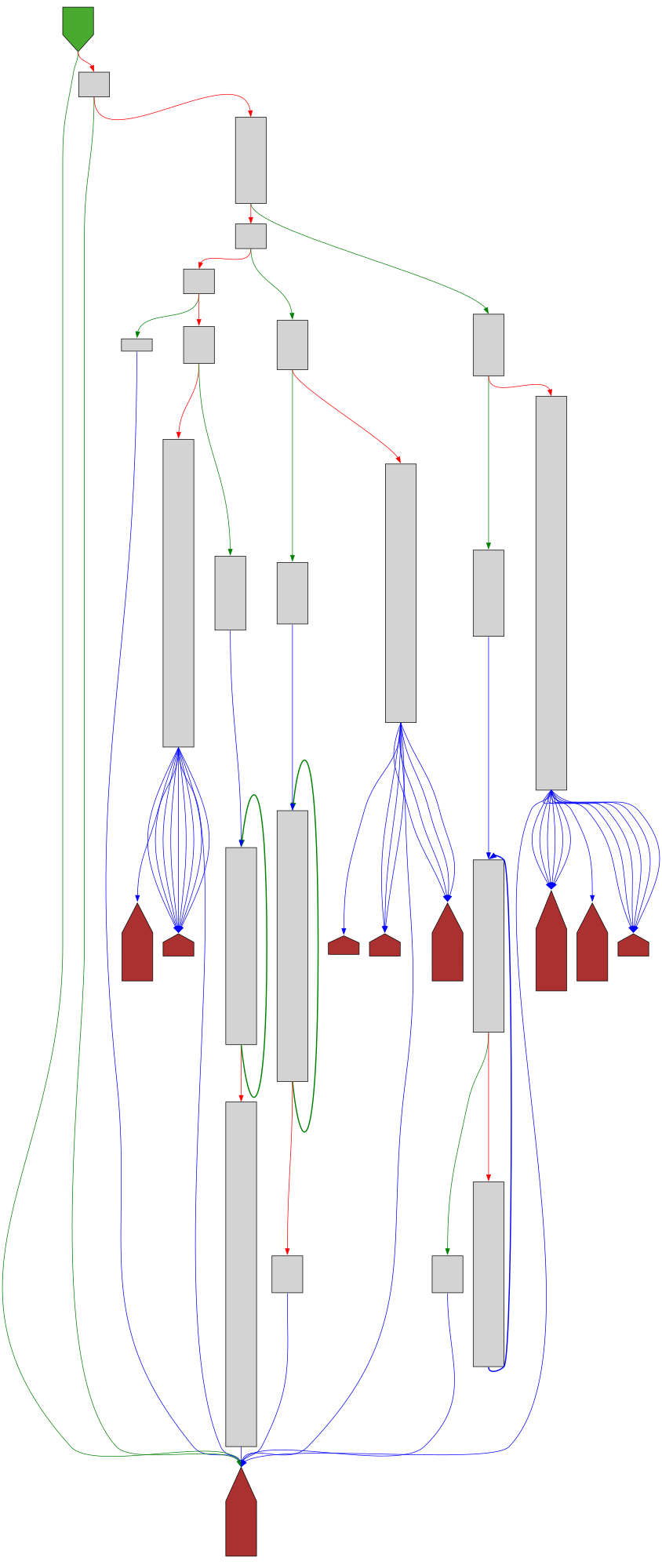
CFG Bot 🤖
cfgbot@mastodon.socialProject: openssl-static-gcc-dwarf 3.4.0
File: openssl
Address: 00714db0
aesni_set_encrypt_key
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00714db0.json&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?graph=https%3A%2F%2Fraw.githubusercontent.com%2Fv-p-b%2Fghidra-function-graph-datasets%2Frefs%2Fheads%2Fmain%2F%2Fopenssl-static-gcc-dwarf%2F00714db0.json&colors=light
buherator
buheratorhttps://seclists.org/oss-sec/2025/q1/45
"It looks like an OEM leaked the patch for a major upcoming CPU vulnerability"
buherator
buheratorhttps://devblogs.microsoft.com/oldnewthing/20250121-00/?p=110788
Zero Day Initiative
thezdi@infosec.exchangeWell that's a first. @ScepticCtf, @diff_fusion), & @SeTcbPrivilege of fuzzware.io used a power drill to gain access to a port and exploit the Autel MaxiCharger. They head off to explain their work - except for the drill - we understand that part. #P2OAuto
K. Reid Wightman  🌻
🌻
reverseics@infosec.exchange
Just upped my donation to my server (if you're on infosec.exchange, here's where to donate, straight from the llama's mouth: https://infosec.exchange/@jerry/109581969726975197 ).
If you're on some other server, find out who runs it, find out if they need financial support to help run it, and donate some money if you can. Servers don't grow on trees. Etc.
blacktop
blacktop@mastodon.socialHigh level diff of iOS 18.3 beta 3 vs. iOS 18.3 RC 🎉
https://github.com/blacktop/ipsw-diffs/blob/main/18_3_22D5055b__vs_18_3_22D60/README.md
RE//verse Conference
REverseConf@infosec.exchangeStruggling to reverse Rust binaries? Cindy Xiao @cdxiao breaks down the Rust type system and shares practical techniques to reconstruct Rust structures. Learn how to tackle Rust malware & analyze binaries like a pro. #REverse2025 #ReverseEngineering #Rust #Malware
Charlie Stross
cstross@wandering.shopPSA FOR AUTHORS: some dipshit put a pirate edition of my latest book on Apple Books with a "50% OFF" medallion on the cover illo. They used an obscure unicode glyph in the author name so that searches for "Charles Stross" find it but the bookstore won't merge it.
Where there's one there'll be others!
My publisher's piracy team is handling it.
If you have a book that came out this year, beware! It's a relative of the IDN homograph attack only targeting ebook stores: