Posts
3368Following
712Followers
1580screaminggoat
screaminggoat@infosec.exchangeHappy #PatchTuesday from Zyxel: Zyxel security advisory for improper privilege management vulnerability in APs and security router devices
CVE-2024-12398 (8.8 high) An improper privilege management vulnerability in the web management interface of the Zyxel WBE530 firmware versions through 7.00(ACLE.3) and WBE660S firmware versions through 6.70(ACGG.2) could allow an authenticated user with limited privileges to escalate their privileges to that of an administrator, enabling them to upload configuration files to a vulnerable device.
There is no mention of exploitation.
Taggart
mttaggart@infosec.exchangeWell dang CVE-2025-21298
This bug rates a CVSS 9.8 and allows a remote attacker to execute code on a target system by sending a specially crafted mail to an affected system with Outlook. The specific flaw exists within the parsing of RTF files.
https://www.zerodayinitiative.com/blog/2025/1/14/the-january-2025-security-update-review
buherator
buheratorAnyhow, if I'll have time I plan to write up why walkmans may be an even better option for kids!
buherator
buheratorEniko (moved ➡ gamedev.place)
eniko@peoplemaking.gameswho came up with january anyway? absolutely awful, useless month, 0/10
Binary Ninja
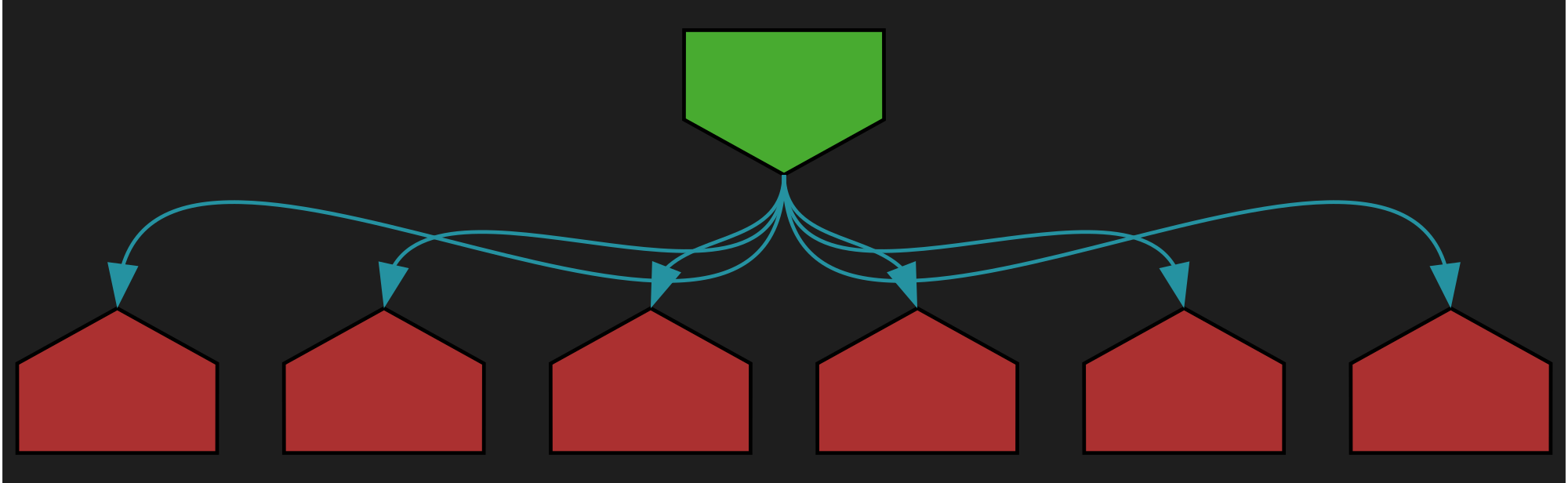
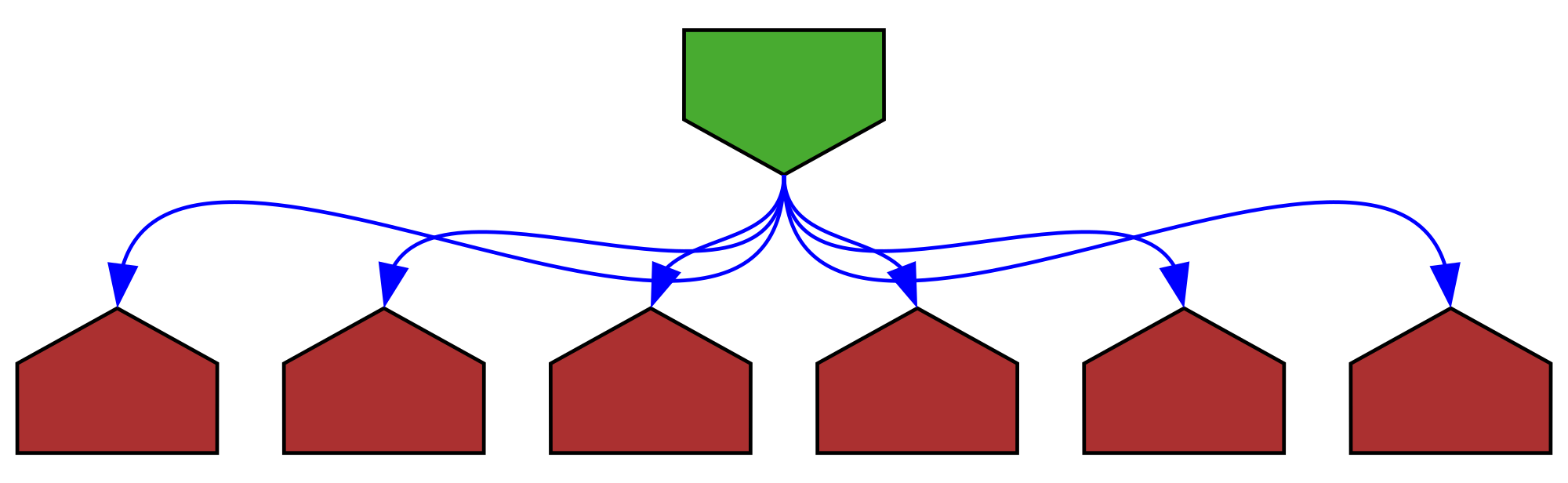
binaryninja@infosec.exchangeNeed to trigger BinExport headlessly to batch process patched binaries (using commercial and above)? First, build for a recent dev or stable: https://gist.github.com/psifertex/31d9bc3167eca91e466ebaae4382521c
Next, install the API for headless: https://docs.binary.ninja/dev/batch.html?h=install_api#install-the-api
Finally, automate your exporting using a script taking advantage of the PluginCommand and PluginCommandContext APIs, like the attached image.
screaminggoat
screaminggoat@infosec.exchangeHappy #PatchTuesday from Ivanti: January Security Update
Bottom line up front: "We have no evidence of any of these vulnerabilities being exploited in the wild."
Links:
- Security Advisory Ivanti Avalanche 6.4.7 (Multiple CVEs)
- Security Advisory - Ivanti Application Control Engine (CVE-2024-10630)
- (AC Engine is present on Ivanti Application Control, Ivanti Neurons for App Control and can integrate with Ivanti Security Controls and Ivanti Endpoint Manager)
- Security Advisory EPM January 2025 for EPM 2024 and EPM 2022 SU6
These are unrelated to the zero-day exploitation of CVE-2025-0282 inside of Ivanti Connect Security, Policy Secure and ZTA Gateways advisory from 08 January 2025.
screaminggoat
screaminggoat@infosec.exchangeThe rest of the #PatchTuesday security advisories from Fortinet:
- Admin Account Persistence after Deletion CVE-2024-47571 (8.1 high)
- Arbitrary file delete on firmware import image feature CVE-2024-33502 (6.5 medium)
- Arbitrary file deletion in administrative interface CVE-2024-32115 (5.5 medium)
- Arbitrary file write on GUI CVE-2024-36512 (7.2 high)
- Blind SQL injection in Update CVE-2024-52969 (4.1 medium)
- Blind SQL injection vulnerability CVE-2023-37931 (8.8 high)
- CVE-2023-4863 - Heap overflow in Chrome/libwebp CVE-2023-4863 ("7.5 high" / NVD 8.8 high)
- bruv I recognize a historical exploited zero-day when I see one: CVE-2023-4863
- Command injection in csfd daemon CVE-2024-46662 (8.8 high)
- Denial of Service in TLS-SYSLOG handler CVE-2024-46667 (7.5 high)
- EMS console login under brute force attack does not get locked CVE-2024-23106 (8.1 high)
- Exposure of sensitive information in RADIUS Accounting-Request CVE-2024-46665 (3.7 low)
- File-Filter Bypass in Explicit Web Proxy Policy CVE-2024-54021 (6.5 medium)
- FortiAP - Restricted Shell Escape via CLI Command Injection CVE-2024-26012 (6.7 medium)
- FortiWeb - Stack overflow in execute backup command CVE-2024-21758 (6.4 medium)
- HTML Content Injection CVE-2024-52967 (3.5 low)
- Hardcoded Encryption Key Used for Named Pipe Communication CVE-2024-50564 (3.3 low)
- Hardcoded Session Secret Leading to Unauthenticated Remote Code Execution CVE-2023-37936 (9.8 critical)
- IPsec dynamic assignation IP spoofing CVE-2023-46715 (5.0 medium)
- Improper Neutralization of Formula Elements in a CSV File CVE-2024-47572 (9.0 critical)
Notes: Other than the zero-day CVE-2024-55591, there is no other mention of exploitation.
Andrew Zonenberg
azonenberg@ioc.exchangeMore details:
Blog post https://ioactive.com/raspberry-pi-2350-hacking-challenge/
I'm also going to be keynoting the HARRIS 2025 Hardware Reverse Engineering Workup at the Max Planck Institute for Security & Privacy in March
Andrew Zonenberg
azonenberg@ioc.exchangeazonenberg@havequick:/tmp$ cat lulz.txt
2024-09-11 17:45 PDT
Successful extraction of RP2350 antifuse bits by FIB PVC
(Random text here to make hash bruteforcing harder)
fjoinzofkjpogkzpofzkpofkspofzpofkz
azonenberg@havequick:/tmp$ sha256sum lulz.txt
a76433af090ceb77b65b153285478bd615bdd51e26a3dd1d6a386b8e1f2ac362 lulz.txt
Talos Vulnerability Reports
talosvulnsWavlink AC3000 wctrls static login vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2024-2034
CVE-2024-39754
Talos Vulnerability Reports
talosvulnsWavlink AC3000 login.cgi Unauthenticated Firmware Upload vulnerability
https://talosintelligence.com/vulnerability_reports/TALOS-2024-2036
CVE-2024-39608
Silent Signal
silentsignal@infosec.exchangeStory of a Pentester Recruitment 2025
https://blog.silentsignal.eu/2025/01/14/pentester-recruitment-2025-mushroom/
screaminggoat
screaminggoat@infosec.exchangeHappy #ZeroDay from your friends at Fortinet: Authentication bypass in Node.js websocket module
CVE-2024-55591 (CVSSv3.1: 9.8 critical) An Authentication Bypass Using an Alternate Path or Channel vulnerability [CWE-288] affecting FortiOS and FortiProxy may allow a remote attacker to gain super-admin privileges via crafted requests to Node.js websocket module.
Please note that reports show this is being exploited in the wild.
Indicators of compromise include possible log entries, IP addresses used, and admin accounts created. cc: @GossiTheDog @wdormann @cR0w @briankrebs
#zeroday #patchtuesday #fortinet #vulnerability #CVE_2024_55591 #infosec #ioc #threatintel #infosec #cybersecurity #
CFG Bot 🤖
cfgbot@mastodon.socialProject: golang/go https://github.com/golang/go
File: src/cmd/compile/internal/reflectdata/reflect.go:1708 https://github.com/golang/go/blob/refs/tags/go1.23.4/src/cmd/compile/internal/reflectdata/reflect.go#L1708
func NeedEmit(typ *types.Type) bool
SVG:
dark https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fcompile%2Finternal%2Freflectdata%2Freflect.go%23L1708&colors=dark
light https://tmr232.github.io/function-graph-overview/render/?github=https%3A%2F%2Fgithub.com%2Fgolang%2Fgo%2Fblob%2Frefs%2Ftags%2Fgo1.23.4%2Fsrc%2Fcmd%2Fcompile%2Finternal%2Freflectdata%2Freflect.go%23L1708&colors=light
Anatoly Shashkin💾
dosnostalgic@mastodon.socialDOOM has now been ported to... a PDF!
(Works in browsers)
https://github.com/ading2210/doompdf
0patch
0patch@infosec.exchangeMicropatches Released for Windows "LDAPNightmare" Denial of Service Vulnerability (CVE-2024-49113)
https://blog.0patch.com/2025/01/micropatches-released-for-windows.html
0patch
0patch@infosec.exchangeMicropatches were issued for fully updated:
- Windows 11 v21H2
- Windows 10 v21H2, v21H1, v20H2, v2004, v1909, v1809, v1803
- Windows 7 - without ESU, or with ESU 1-3
- Windows Server 2012, Server 2012 R2 - without ESU
- Windows Server 2008 R2 - without ESU, or with ESU 1-4
We would like to thank Or Yair (@oryair1999) and Shahak Morag of @safebreach for sharing their analysis and proof-of-concept, which made it possible for us to create a micropatch for this issue. We'd also like to thank the original finder Yuki Chen (@guhe120).
daniel:// stenberg://
bagder@mastodon.socialTurns out snprintf() in old Windows C runtimes is documented to have the buffer overflow that no other implementations do. 🤔