Posts
3035Following
701Followers
1550cts🌸
gf_256@bird.makeupNew attack on x86 secure enclaves, specifically AMD SEV this time. SEV is AMD's answer to Intel TDXs.
Basically tricking the CPU into thinking the DRAM is a different size, causing physical address aliasing, which can then be exploited
"Your GitHub account now includes free use of GitHub Copilot"
LOL get fucked
abadidea
0xabad1dea@infosec.exchangeWhy do iOS apps update so much. “Bug fixes and improvements.” You’ve said that every week for eight years. I’m impressed by the commitment honestly but what are you DOING in there
SwiftOnSecurity
SwiftOnSecurity@infosec.exchangeBiden has just pardoned the entire executive team behind the Windows 11 out of box experience.
Caitlin Condon
catc0n@infosec.exchangeAlmost exactly a year ago, Rapid7 put out a technical analysis of Apache #Struts 2 CVE-2023-50164 that said:
* Exploit payloads were going to need to be customized to the target
* It wasn't clear that there was any critical mass of remotely exploitable applications out of the box
* The reports of exploitation in the wild all appeared to be unsuccessful attempts rather than IRL compromises of production systems.
https://attackerkb.com/topics/pe3CCtOE81/cve-2023-50164/rapid7-analysis
Fast-forward to CVE-2024-53677 and we can repeat the above verbatim, with one pretty notable exception — the "fixed" version that ostensibly remediates the vulnerability actually doesn't, and code-level changes are required (to migrate away from the vulnerable file upload interceptor) to actually remediate it. Also the "fixed" release (6.4.0) appears to have gone out a year ago? No idea. Big ups to @fuzz for the analysis!
https://attackerkb.com/assessments/28f08c0a-702c-4ab0-99cb-eea00202fa2c
screaminggoat
screaminggoat@infosec.exchangeCVE-2023-34990 is credited to @hacks_zach of Horizon3.ai. This gave me a starting point for figuring out where to look for information. It's contained in Fortinet FortiWLM Deep-Dive, IOCs, and the Almost Story of the “Forti Forty” posted on 14 March 2024.
It is described as an unpatched vulnerability: "Unauthenticated Limited Log File Read – Allows retrieval of arbitrary log files which contain administrator session ID tokens" Check out the Path to Remote Code Execution #2 section for vulnerability details:
This vulnerability allows remote, unauthenticated attackers to access and abuse builtin functionality meant to read specific log files on the system via a crafted request to the /ems/cgi-bin/ezrf_lighttpd.cgi endpoint. This issue results from the lack of input validation on request parameters allowing an attacker to traverse directories and read any log file on the system.
Based on the details of the blog, I can confidently say that the new CVE and the blog's vulnerability are almost certainly one and the same.
cc: @GossiTheDog @jerry
#CVE_2023_34990 #fortinet #fortiwlm #vulnerability #CVE #infosec #cybersecurity
kcarruthers
kcarruthers@mastodon.socialHIV breakthrough: drug trial shows injection twice a year is 100% effective against infection
http://theconversation.com/hiv-breakthrough-drug-trial-shows-injection-twice-a-year-is-100-effective-against-infection-233295
screaminggoat
screaminggoat@infosec.exchange@cR0w I found it. I found the vulnerability details: https://www.horizon3.ai/attack-research/disclosures/fortiwlm-the-almost-story-for-the-forti-forty
Unauthenticated Limited Log File Read – Allows retrieval of arbitrary log files which contain administrator session ID tokens
"CVE-2024-???? (0-day): Fortinet FortiWLM Unauthenticated Limited File Read Vulnerability"
This vulnerability allows remote, unauthenticated attackers to access and abuse builtin functionality meant to read specific log files on the system via a crafted request to the /ems/cgi-bin/ezrf_lighttpd.cgi endpoint. This issue results from the lack of input validation on request parameters allowing an attacker to traverse directories and read any log file on the system.
Alexandre Dulaunoy
adulau@infosec.exchangeIf you are wondering about the unpublished CVE-2024-49848... there is a PoC.
🔗 https://vulnerability.circl.lu/comment/23fd524b-475e-4b9f-8dc2-7b67f4cec409
buherator
buheratorbuherator
buheratorhttps://www.bloomberg.com/news/articles/2024-12-18/us-probes-china-founded-router-maker-on-national-security-fears
TP-Link about join the club of Huawei&Kaspersky
#frombsky
Craig Grannell
craiggrannell@mastodon.socialUK: “It’s still illegal to rip a CD you legally own to MP3!”
Also UK: “Hey, let’s exempt those AI guys from copyright law!”
FFS.
https://www.gov.uk/government/consultations/copyright-and-artificial-intelligence
Open Web Docs
openwebdocs@front-end.socialLearn about XSS for XMAS!
We created a new MDN page about Cross-site scripting: https://developer.mozilla.org/en-US/docs/Web/Security/Attacks/XSS
cpresser
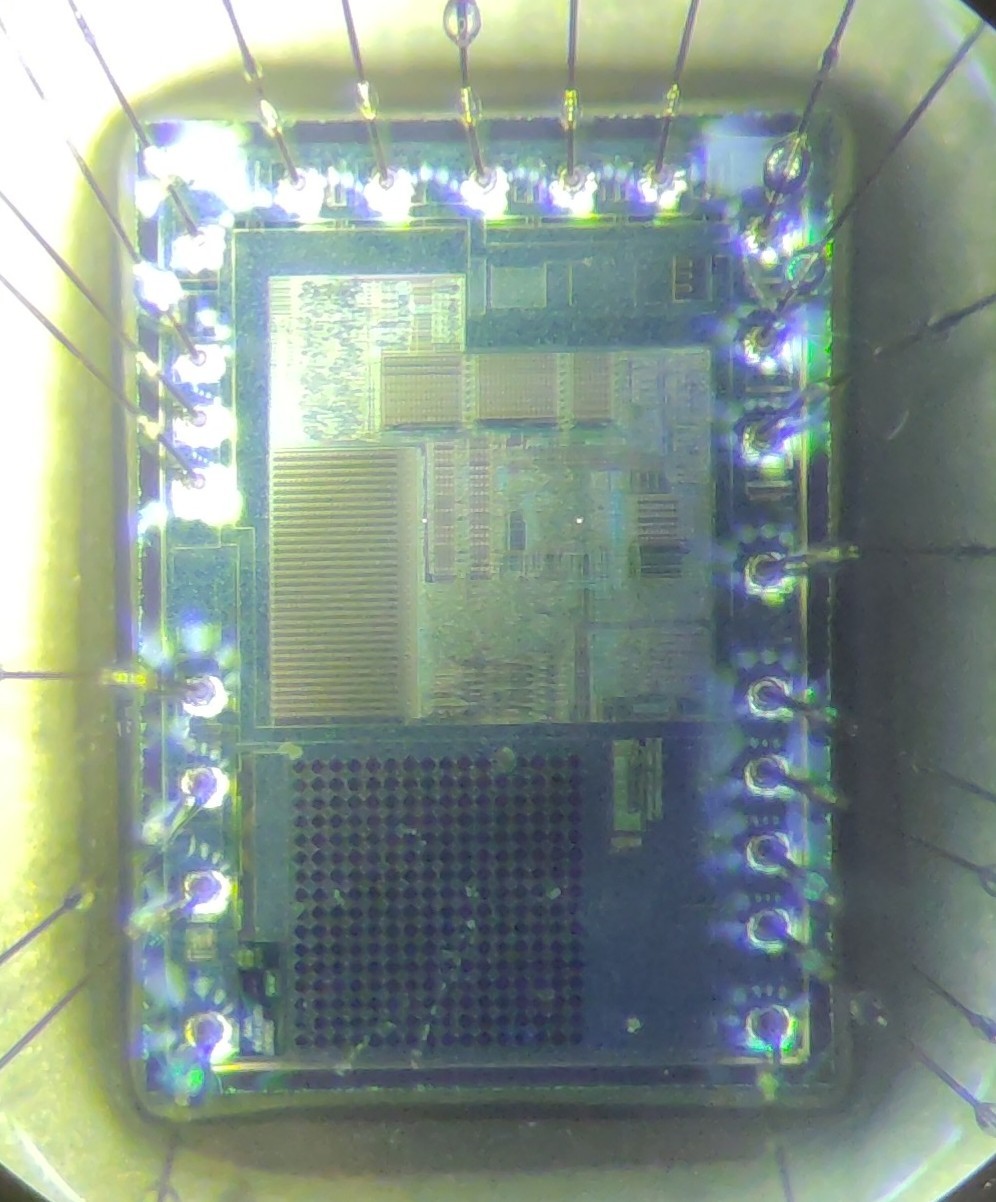
cccpresser@chaos.socialHere is another #NameThatWare challenge. This time I am quite sure that no text or marking needs to be blurred.
Do you know what this thing is? Can you name the exact part number or product name?
As always, explain your guess/deduction and hide it behind a CW to not spoil others.
buherator
buheratorbuherator
buheratorhttps://www.youtube.com/watch?v=0f_TbyIIPnc
#hardstyle
✧✦Catherine✦✧
whitequark@mastodon.socialgame i would like to play: Factorio but you *only* do compliance paperwork
HalvarFlake
HalvarFlake@mastodon.socialI am mildly amused that OpenAI telemetry rollout led to a classical Kubernetes control plane DoS.
In my experience DDoSing your own control plane is the #1 way people generate large failures in K8s. What are others?