Posts
3037Following
703Followers
1550buherator
buheratorbuherator
buheratorESET Research
esetresearch@bird.makeupUPDATE: #ESETresearch was contacted by one of the possible authors of the Bootkitty bootkit, claiming the bootkit is a part of project created by cybersecurity students participating in Korea's Best of the Best (BoB) training program. 1/2
https://www.welivesecurity.com/en/eset-research/bootkitty-analyzing-first-uefi-bootkit-linux/
Open Source Security mailing list
oss_security@bird.makeupPerl interpreter patch to issue runtime warnings against suspicious two-argument open() calls https://www.openwall.com/lists/oss-security/2024/12/04/1
screaminggoat
screaminggoat@infosec.exchangeSonicWall security advisory 03 December 2024: SonicWall SMA100 SSL-VPN Affected By Multiple Vulnerabilities
- CVE-2024-38475 (7.5 high) Path traversal vulnerability – attributed to publicly known Apache HTTP Server vulnerability
- CVE-2024-40763 (7.5 high) SonicWALL SMA100 Heap-based buffer overflow vulnerability
- CVE-2024-45318 (8.1 high) Stack-based buffer overflow vulnerability
- CVE-2024-45319 (6.3 medium) Certificate-based authentication bypass
- CVE-2024-53702 (5.3 medium) Insecure randomness 🤪
- CVE-2024-53703 (8.1 high) Stack-based buffer overflow vulnerability
There is no evidence that these vulnerabilities are being exploited in the wild
#sonicwall #sma #sslvpn #vulnerability #CVE #infosec #cybersecurity
buherator
buheratorIs there an archive of Packet Storm's data available somewhere?
RE: https://mastodon.ie/@ciaranmak/113600017990303470
buherator
buheratorhttps://labs.watchtowr.com/where-theres-smoke-theres-fire-mitel-micollab-cve-2024-35286-cve-2024-41713-and-an-0day/
Almond OffSec
AlmondOffSec@infosec.exchange@sigabrt @yeswehack This issue was assigned CVE-2024-52531. While the CVE description states that the vulnerability cannot be reached from the network, it seems, in fact, possible (check the blogpost for details).
Almond OffSec
AlmondOffSec@infosec.exchangeTeam member @sigabrt describes a fuzzing methodology he used to find a heap overflow in a public @yeswehack bug bounty program for Gnome: https://offsec.almond.consulting/using-aflplusplus-on-bug-bounty-programs-an-example-with-gnome-libsoup.html
buherator
buheratorShow content
cpresser
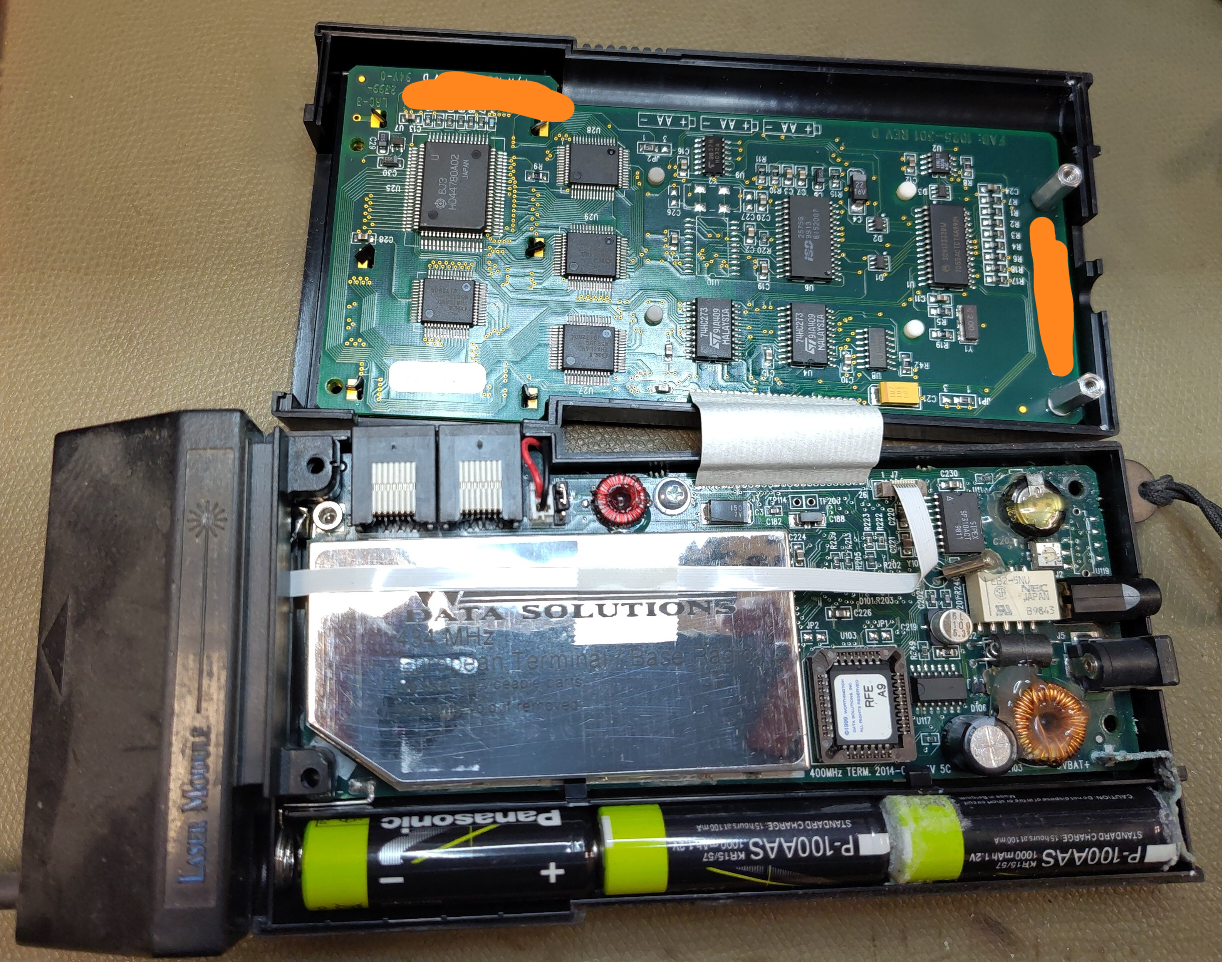
cccpresser@chaos.socialHere is a new #NameThatWare challenge.
Please don't just guess into the blue, try to deduct what it is, write down your observations and thoughts.
Hide your answer behind a CW to not spoil it for other participants.
buherator
buheratorProject Zero Bot
p0botWindows Kernel double-fetch in the loading of remote registry hives, leading to memory corruption
https://project-zero.issues.chromium.org/issues/42451731
CVE-2024-43452
Dan Gillmor
dangillmor@mastodon.socialAs @daringfireball writes, Google is lying through its corporate teeth about its claims to be encrypting messages.
https://daringfireball.net/linked/2024/12/04/shame-on-google-messages
What a slimy company Google has become, so far distant from its early days when it was so admirable.
runZero, Inc
runZeroInc@infosec.exchange‼️ New vulnerabilities have been disclosed in the Veeam Service Provider Console.
CVE-2024-42448 is critical, potentially allowing remote code execution. CVE-2024-42449 is rated high, potentially leaking the NTLM hash of a service account & allowing file deletion.
Learn more and see how to find potentially impacted systems:
Clément Labro
itm4n@infosec.exchangeI updated the diagram representing the different Point and Print configurations and their exploitation on my blog.
Hopefully, this should provide a better understanding of the whole "PrintNightmare" situation to both defenders and red teamers. 🤞
Adam Shostack 

adamshostack@infosec.exchange
New blog: Risk talk at JPL
Before Thanksgiving, I was in Southern California, and I was honored to be able to give a talk at the Jet Propulsion Lab. The talk is titled “Threat Modeling: Engineering and Science.” The first part of the talk puts threat modeling in context for engineering secure systems, while the second part considers why we do what we do and asks some questions about how we think about risk.