Posts
3033Following
701Followers
1550A bit more gasoline to pour into Clownstrike's fire... ;-)
zhenech
zhenech@chaos.socialAnyone can Access Deleted and Private Repository Data on GitHub ◆ Truffle Security Co.
https://trufflesecurity.com/blog/anyone-can-access-deleted-and-private-repo-data-github
Haifei Li
haifeili@bird.makeupCongrats @nachoskrnl for being nominated @pwnieawards for his 3-episode research work on Windows paths - well deserved (yes, I nominated it:)).
https://x.com/PwnieAwards/status/1815894380789592298
Samuel Groß
saelo@chaos.socialSomething I've had on my list for quite some time and finally got around to now: updating the HowFuzzilliWorks document: https://github.com/googleprojectzero/fuzzilli/blob/main/Docs/HowFuzzilliWorks.md
Besides a number of smaller changes (e.g. new mutators), the design of the HybridEngine has changed considerably since the document was initially written.
Happy fuzzing!
Sebastian
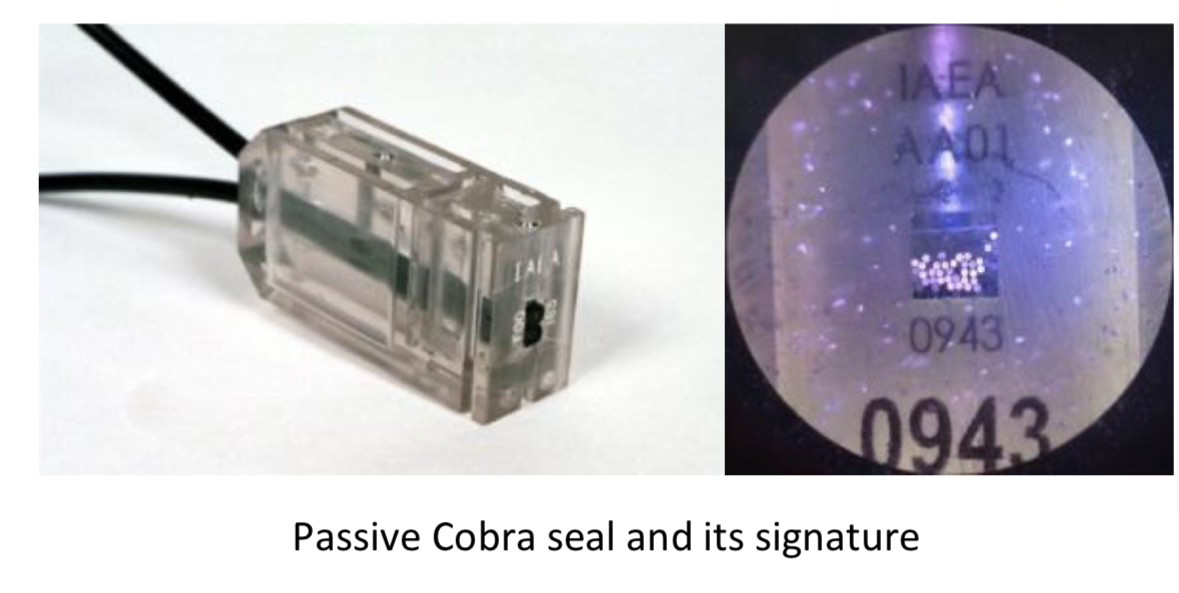
moehrenfeld@social.karotte.org#TIL that the #IAEA uses something called a „COBRA seal“ to seal relevant objects against manipulation. One type of these seals works by using a multi-core optical cable. When the seal is locked a random number of cores are cut. This creates a unique optical pattern that can be verified simply by shining a light into the cable and can’t be recreated.
The Verge
verge@mastodon.socialThe moral bankruptcy of Marc Andreessen and Ben Horowitz https://www.theverge.com/2024/7/24/24204706/marc-andreessen-ben-horowitz-a16z-trump-donations
Kevin Beaumont
GossiTheDog@cyberplace.socialThe initial Post Incident Review is out from CrowdStrike. It’s good and really honest.
There’s some wordsmithing (eg channel updates aren’t code - their parameters control code).
The key take away - channel updates are currently deployed globally, instantly. They plan to change this at a later date to operate in waves. This is smart (and what Microsoft do for similar EPP updates).
https://www.crowdstrike.com/falcon-content-update-remediation-and-guidance-hub/
hanno
hanno@mastodon.socialDo I know anyone with a mail address on a mail server managed by barracuda networks who would help me with something? I'd like to test a few things (just sending you a few test mails and see if they arrive).
BrianKrebs
briankrebs@infosec.exchangeWild, true story from the security awareness and training company KnowBe4 that details how they inadvertently hired a North Korean hacker who was posing as a Western tech worker.
Kudos to them for publishing this. If it can happen to a security awareness company, it can happen to anyone (full disclosure: they've been an advertiser on my site for ages).
https://blog.knowbe4.com/how-a-north-korean-fake-it-worker-tried-to-infiltrate-us
DoI
DoI@mastodon.nzI've published a little blog on binary patching Golang produced assembly to alter the stdlib net/http functionality. #golang and #infosec frens maybe interested! https://pulsesecurity.co.nz/articles/golang-patching
Doyensec
doyensec@infosec.exchangeWe're proud our testing helps ensure the security of Thinkst's OSS Canary Tokens! As part of their transparency efforts, you can read the results of our latest round of testing here:
https://www.doyensec.com/resources/Doyensec_ThinkstCanaryTokensOSS_Report_Q22024_WithRetesting.pdf
screaminggoat
screaminggoat@infosec.exchangeCISA: CISA Adds Two Known Exploited Vulnerabilities to Catalog
Hot off the press! CISA adds two vulnerabilities to the KEV Catalog:
- CVE-2012-4792 (CVSSv2: 9.3 "high") Microsoft Internet Explorer Use-after-free vulnerability
- CVE-2024-39891 (5.3 medium) Twilio Authy Information Disclosure Vulnerability
#CISA #KEV #knownexploitedvulnerabilitiescatalog #CVE_2012_4792 #CVE_2024_39891 #eitw #activeexploitation #CVE #vulnerability
/r/netsec
_r_netsec@infosec.exchangeCVE-2019-8805: Apple EndpointSecurity framework Privilege Escalation https://blog.securelayer7.net/applied-endpointsecurity-framework-previlege-escalation/
Sabrina has moved!
sabi@infosec.spaceBlog posts should always include a first published date and a last edited date.
Royce Williams
tychotithonus@infosec.exchangeWas ILOVEYOU worse than CrowdStrike?
https://en.m.wikipedia.org/wiki/ILOVEYOU
Looks like more hosts were affected by ILOVEYOU (45 million in the first 24 hours) ... but the damage was somewhat more random because files were overwritten.
And now that there is a well-known CrowdStrike recovery procedure, as long as you follow it, you're okay -- but if you didn't have good backups, files overwritten by ILOVEYOU were unrecoverable.
Taggart 
mttaggart@infosec.town
Any event that makes the front page of a news outlet will be used as a phishing lure.
Any “threat intelligence” that alerts you to this is next to useless.
Stefano Marinelli
stefano@bsd.cafeEmail received a few days ago: "We need to know which version of SSH is installed on the server, as we want to ensure it is not vulnerable to external attacks." My response: "Don’t worry, SSH is accessible ONLY via VPN, and I am the only one with access to that VPN—activated only when needed—so there is no way for there to be any issues, regardless of the version used."
Email received this morning: "We’re not interested; you must provide the SSH version installed and, if it's not the latest, ensure us of the update date."
My response: "Sorry, could you explain the rationale? SSH is not exposed, it’s not listening on any public IP."
Their reply: "Provide the version."
My response: "OpenSSH_9.7, LibreSSL 3.9.0, on OpenBSD."
Their reply: "This is not considered secure. It must be OpenSSH_9.2p1 Debian-2+deb12u3."
My response: "It’s not Debian; it’s OpenBSD."
Their reply: "So the systems are insecure."
And they claim to be a cybersecurity company...
#CyberSecurity #SSH #VPN #ITSecurity #SysAdmin #TechSupport #OpenBSD #Debian
❄️☃️Merry Jerry🎄🌲
jerry@infosec.exchange@masek we know a few other things:
The channel file update that caused this problem was for detecting malicious named pipe usage on the system by the CS kernel module
These channel file updates are pushed a few times per day.
The implication there, at least for me, is that the QA process is almost certainly entirely automated.
I have to believe that the release process probably doesn’t depend on someone doing a set of steps during the push process, including QA
I have two hypotheses:
a) the release pipeline doesn’t account for testing on a windows system that is crashed by an update and never comes back to life.
Or
b) the release pipeline doesn’t test channel file updates after they’ve been encoded for each customer, and it was some interplay between the content of the update, the encoding process, and a logic bug in the parser that resulted in the problem.
Also, on the topic of the terms and conditions preventing use for life safety situations - that is quite standard practice in the US, given how litigious we are. Most software and most services have some similar variation - I know we did at my prior employer, so I wouldn’t read too much into that.