Will Dormann
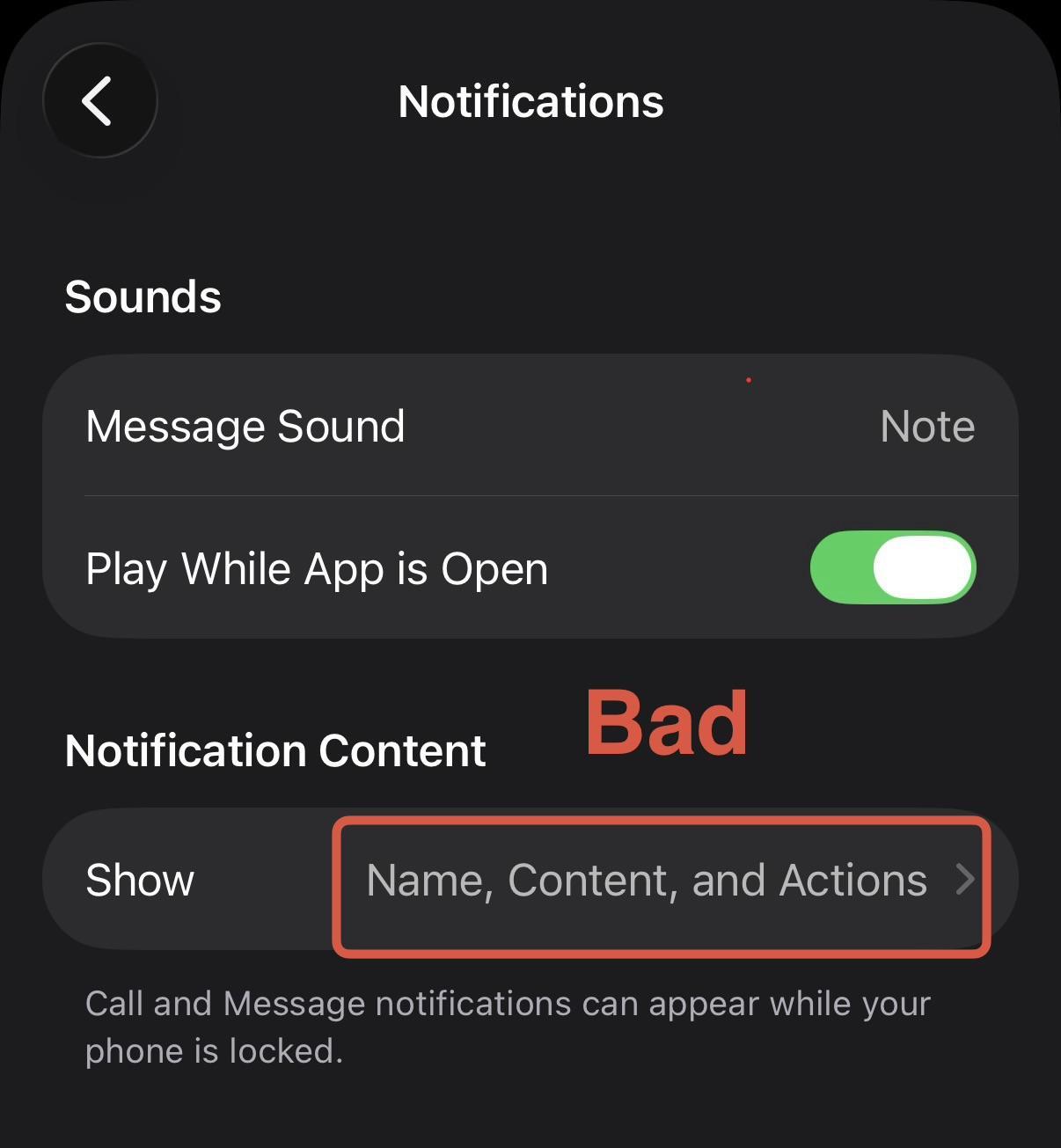
wdormann@infosec.exchangeLet me get this straight...
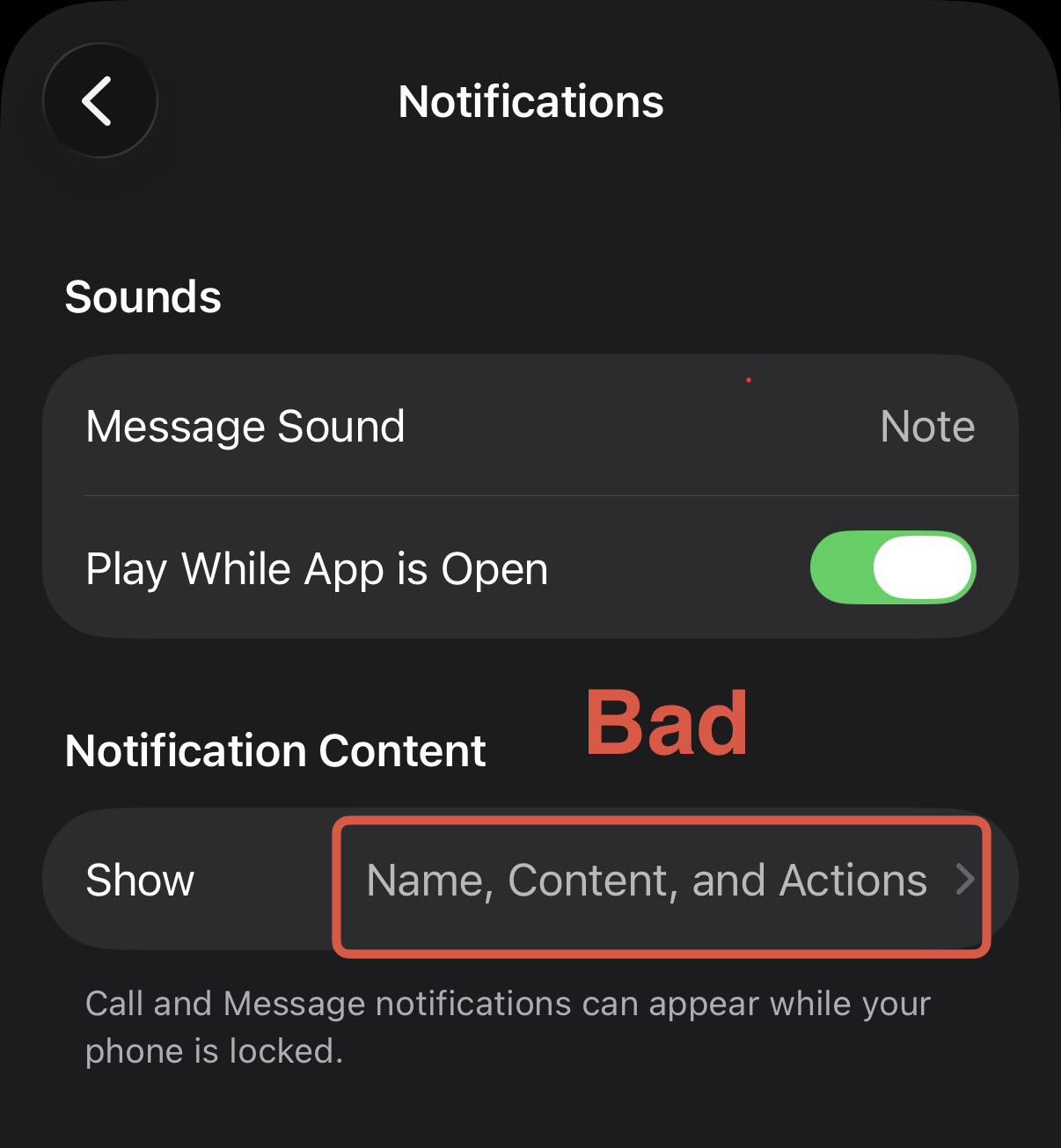
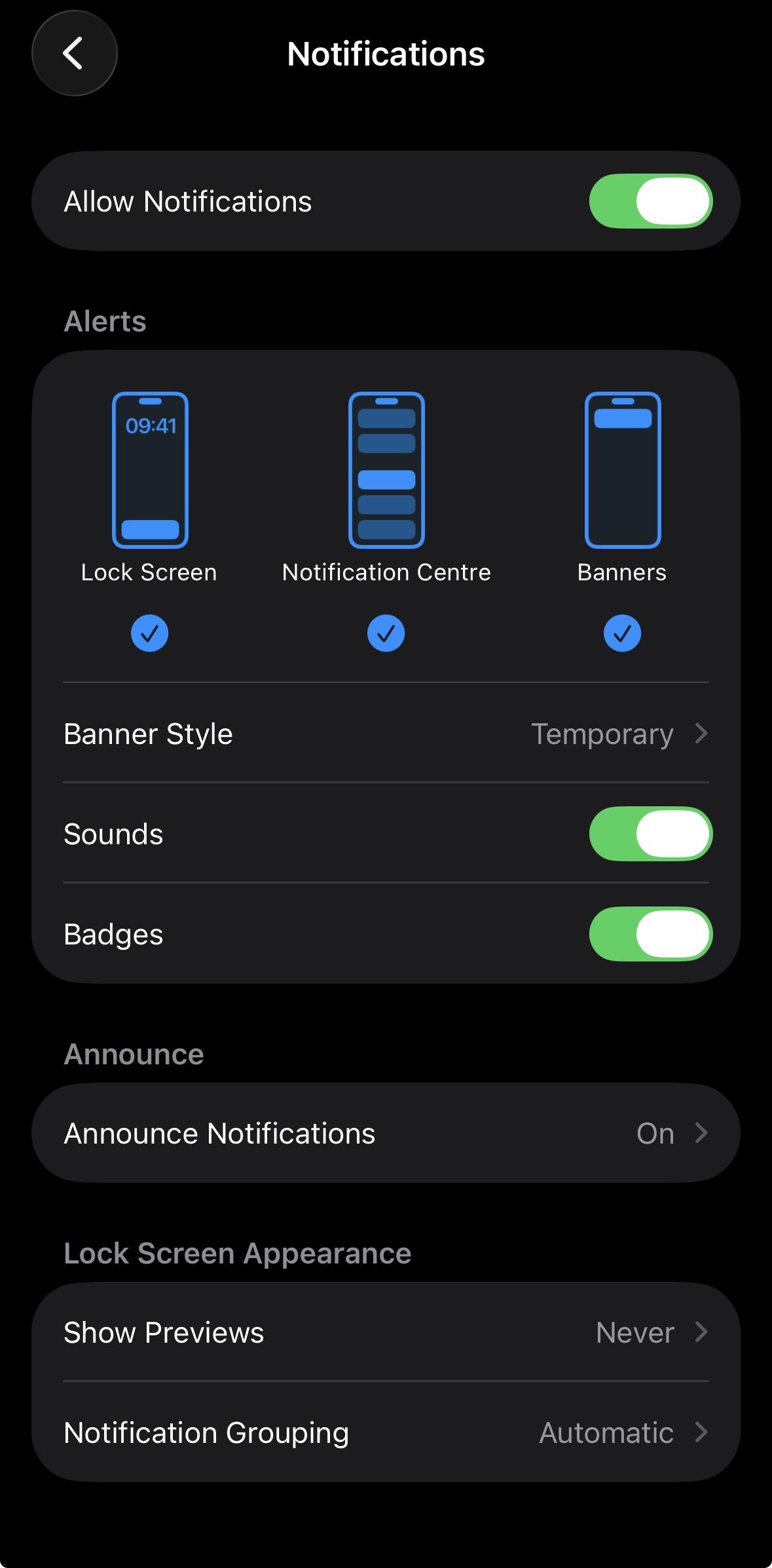
The default setting for Signal on an iPhone allows law enforcement to see the content of all incoming messages, even after the app has been deleted? 🤔
glitchim
bsod@framapiaf.org@wdormann how the FBI could access the device notifications database?
Will Dormann
wdormann@infosec.exchange@bsod
They had access to an unlocked device.
Unclear whether that was voluntary, through coercion, or through trickery like Cellebrite advertises.
0mnicore
omnicore@ieji.de@wdormann Lockdown mode overrides this setting. Or if you don’t use lockdown mode (which is a bad choice) you should change it in Signal. @signalapp cannot account for iPhone’s default behaviour (keeping a record of notifications)
Will Dormann
wdormann@infosec.exchange@omnicore @signalapp
Yeah, I've been on Lockdown Mode since it was released.
Do you have a reference for how this is the case?
⠠⠵ avuko
avuko@infosec.exchange@wdormann The default setting for the iPhone by the US company Apple is to pass messages through to their Notification functionality.
They could be retrieved by the FBI from the US company Apple's push notification database.
The US company Apple, not Signal, has a shoddy security model here.
PS: To any Apple fanboys who can't stand a single bad word about Apple, I'll block you permanently and happily if you even give a squeak.
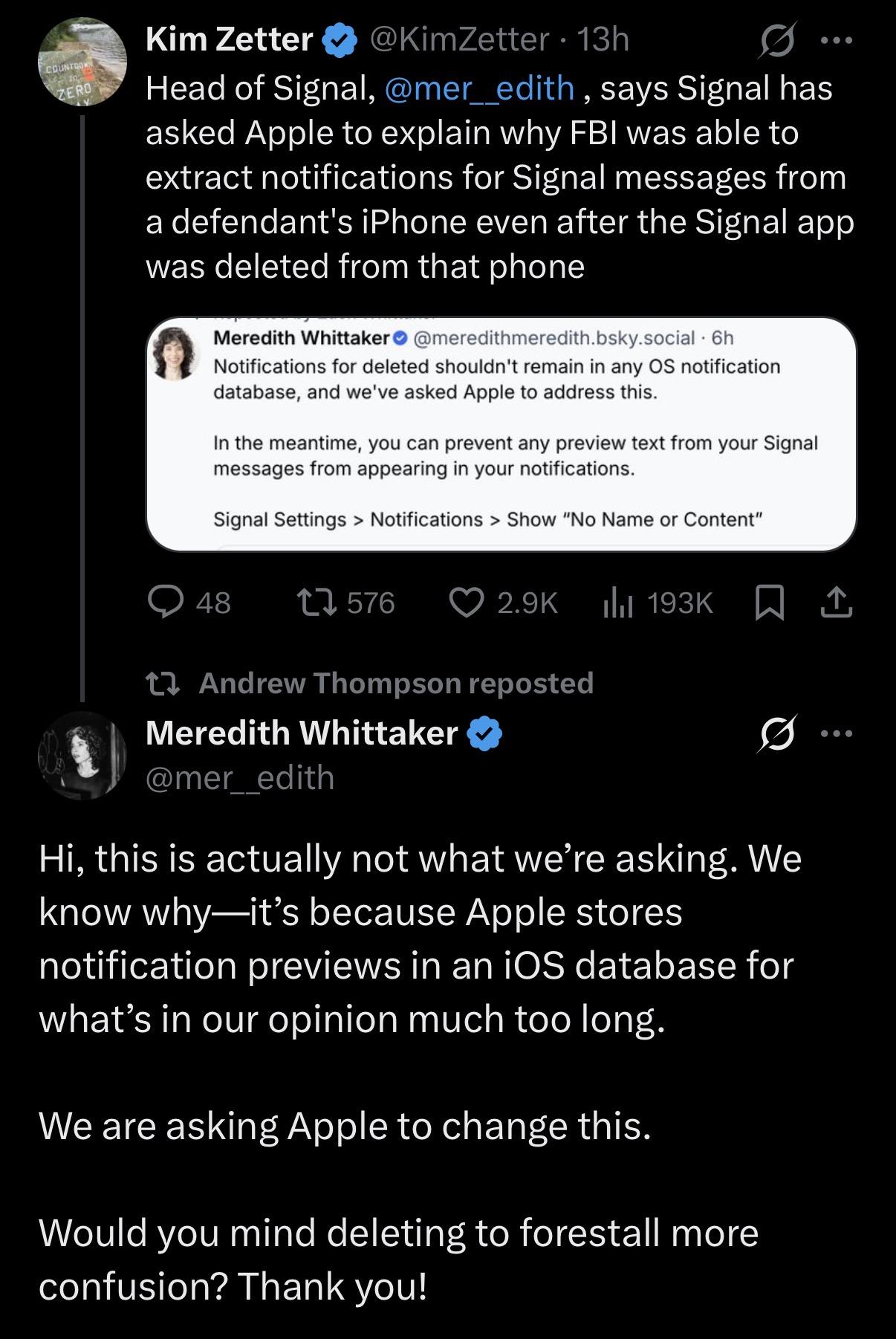
Will Dormann
wdormann@infosec.exchange@Mer__edith
Can we get a comment on this?
1) The default Signal setting to show message contents in push notifications seems... bad, assuming this article is accurate.
2) Does changing the in-Signal-app setting for Notification Content indeed prevent notifications from being stored anywhere, which by default contains incoming message bodies.
Will Dormann
wdormann@infosec.exchange@omnicore @signalapp
Regardless, even just testing things out on a clean test device, an iPhone with Lockdown Mode enabled still gets push notifications with the incoming message body.
So, color me skeptical that Lockdown Mode does anything regarding this.
⠠⠵ avuko
avuko@infosec.exchange@Beachbum @wdormann if you do not want to be tracked/traced/placed, don’t bring a mobile phone in any way tied to you or your previous locations.
I worked in telco for years, trust me on this one.
The problem here was different: people who thought they were communicating privately, had their messages (or those that ended up in Apple’s notifications database on the iPhone) accessible to law enforcement. Even after (taking precautions like) deleting the app.
Awkward Turing
AwkwardTuring@infosec.exchange@wdormann what does that mean for any other app that pushes sensitive data as notifications? Wondering if disabling the notification rly disables the storing in the DB or just the display of it.
Will Dormann
wdormann@infosec.exchange@AwkwardTuring
Right. That's the million dollar question.
C++ Wage Slave
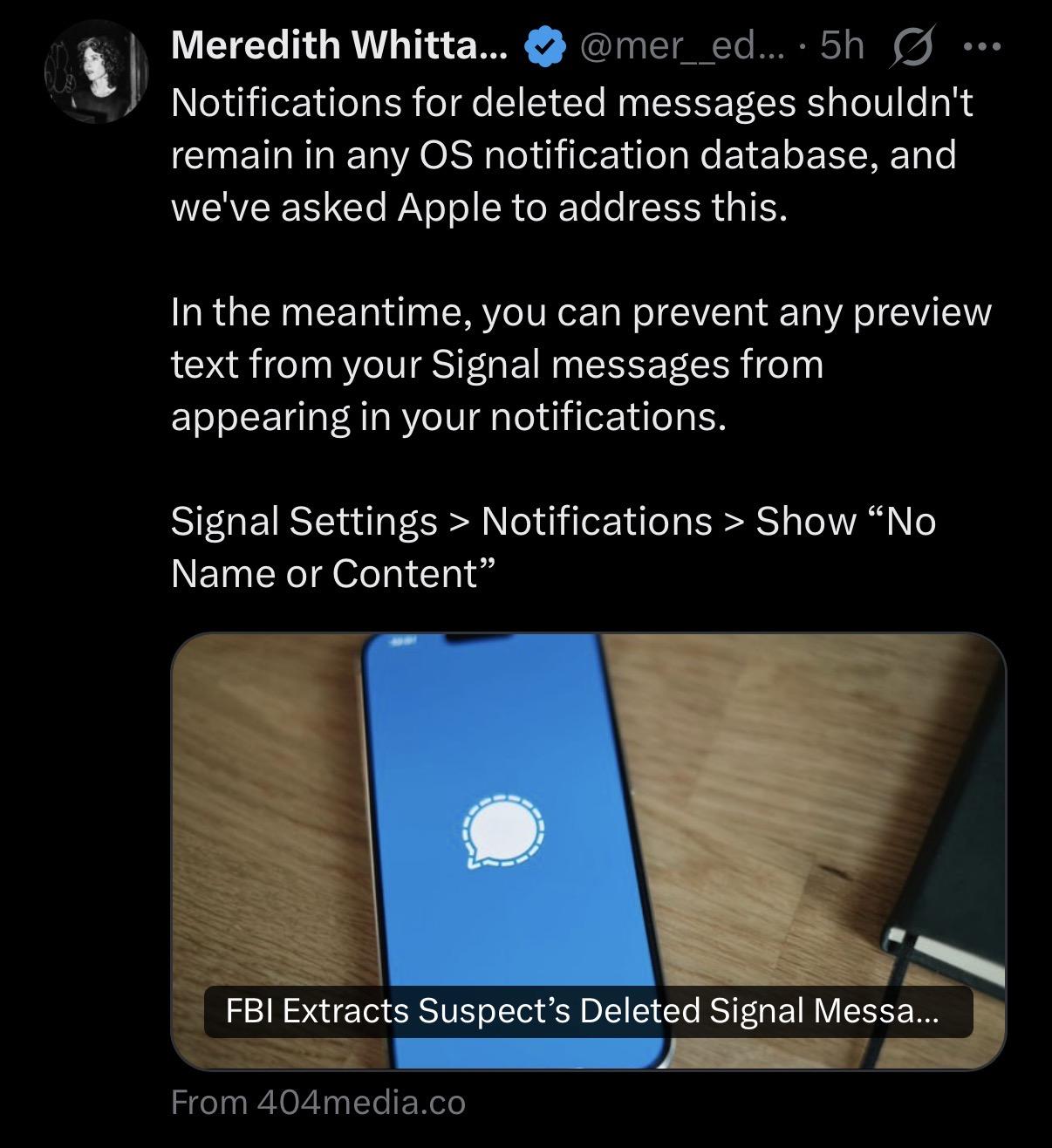
CppGuy@infosec.spaceOh, but it's even worse than that. From TFA:
Authorities have turned to push notifications more broadly as an investigative strategy too; in June 404 Media reported Apple gave governments data on thousands of push notifications. Those were legal demands made to Apple, while the Prairieland case was about data from a device authorities had physical access to.
This suggests that your #notifications are sent home to #Apple. Why is that necessary?
I have further questions:
- Why, and for whose benefit, were notifications stored on the phone after the #Signal app had been removed? They were useless to the other of the phone.
- How much of this vulnerability is shared with Android phones?
Timo P.
tdpsk@sueden.social@wdormann @Mer__edith I was unaware notifications on iOS were stored in an on-device database even after they had been dismissed. That seems like an inefficient waste of storage - does anybody have a link to some Apple docs providing context about this database?
Drew Mochak
prism@infosec.exchange@wdormann The default setting is that you get notified when you receive a message, because most people want those.
Daniel Fisher(lennybacon)
lennybacon@infosec.exchange@wdormann Looks different here. But it’s Most probably the „Preview“ -Thing that causes Information to leak (to the OS which persists it unsecure)
Beachbum
Beachbum@mastodon.sdf.org@avuko @wdormann That’s partly why I’m asking because I disable notifications as soon as I purchase a phone. Locating my phone is important because I misplace it a lot. My location services it’s also always off.
I have a degree in IT, but it goes back to 2006 and so much has changed since then and honestly, I only keep up through what I read here on Mastodon. I thought doing these things would secure my privacy.
⠠⠵ avuko
avuko@infosec.exchange@Beachbum @wdormann I’m also becoming less and less well versed in all things phone/telco, but location tracking, and device/ SIM/ ID combos are the bread and butter of mobile phones and telcos.
From billing to getting the message to you, they can’t do it without that info.
On top of that you have what the phone vendors do, and what the apps on the phone do, and where that data is stored, and who has access, and how one of these parties can access info of another like in the current case.
It is almost impossible to track, certainly because our mobile phones are all black boxes to almost all people that use them.
Anyway, there are okay manuals online, and remember:
Will Dormann
wdormann@infosec.exchange@lennybacon
The screenshot I shared is from the Signal app itself, in Settings.
Not iPhone-wide settings.
Will Dormann
wdormann@infosec.exchange@prism
The default setting is that you get notified with the message contents
Will Dormann
wdormann@infosec.exchange@tdpsk @Mer__edith
The problem is that such content is not included in unencrypted backups. So we mortals can't even confirm this, as we don't have access to full-device exploit tools such as Cellebrite.
f*cking b*tch club
grammasaurus@mastodon.social@omnicore @wdormann @signalapp What I got from the article is what you said here: the weakness is in iPhone’s default behavior.
Will Dormann
wdormann@infosec.exchange@grammasaurus @omnicore @signalapp
The screenshot I shared is from the Signal app itself, which chooses to include the message content in notifications.
So I'd say that both are at fault.
Will Dormann
wdormann@infosec.exchangeApple gave governments data on thousands of push notifications
Is open to wide interpretation. Did they give information about thousands of push notifications? (i.e. metadata) (e.g. the App that sent the notification and the timestamp, and potentially account info tied to the request)
If they gave the actual notification content, then that's a whole other scandalous animal. Extraordinary claims require extraordinary evidence, and whatnot.
lazarus7
lazarus7@infosec.exchange@wdormann switching my friends and family to signal was made easier because of settings like this. It behaves like a normal messaging app. None of them have a threat model that has them thinking of device seizure by law enforcement.
Will Dormann
wdormann@infosec.exchange@thomasareed @Viss
I don't believe you, as that setting (my screenshot) is within the Signal app itself.
As such, if they wanted a different default value, they would have just released the software with the preferred setting.
Thomas Reed
thomasareed@infosec.exchange@wdormann @Viss Okay, whatever. “I don’t believe you” is a pretty rude response, as it implies I’m lying and that nothing changed in the years since I installed it. I do distinctly remember some kind of warning about Signal notifications from somewhere, though, so this is most definitely NOT new news.
Daniel Fisher(lennybacon)
lennybacon@infosec.exchange@wdormann Thanks. Looks the same in the app to me.
Probably the same but configured from the opposite side of things.
Will Dormann
wdormann@infosec.exchange@Mer__edith
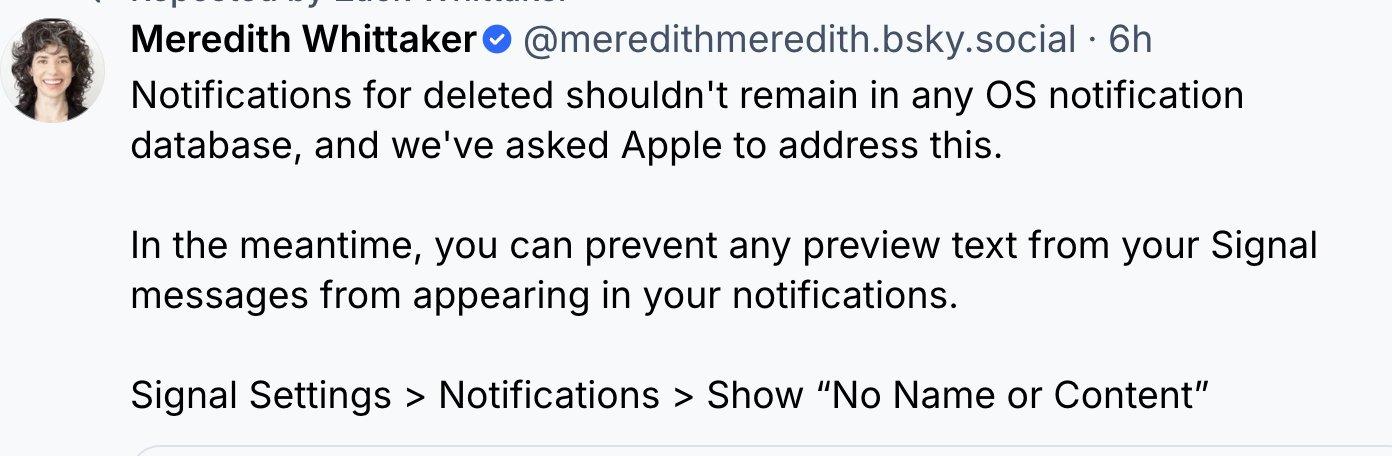
On the macOS side of things, we have confirmation that Signal notification contents get stored, even for disappearing messages
iOS sadly offers less visibility into what's going on. But the FBI probably appreciates that it's happening there too.
The default notification setting for Signal (on both iOS and macOS) ensures that potentially sensitive information leaks out of the Signal app. This is unfortunate.
f*cking b*tch club
grammasaurus@mastodon.social@wdormann @omnicore @signalapp That’s not at all what I see on my phone for the signal app.
I’m using iOS 18.1.1–maybe the latest version has changed a lot?
Will Dormann
wdormann@infosec.exchange@grammasaurus @omnicore @signalapp
18.1.1, eh? If you don't install security updates, I wouldn't expect your experience to be like the rest of the world. 😂
Timo P.
tdpsk@sueden.social@wdormann @Mer__edith from what I understand it was forensically recounstructed from storage, the database itself is non-persistent (on the software layer). So something Apple could solve in a future update, e.g. by regularly properly wiping that part of storage.
Will Dormann
wdormann@infosec.exchange@tdpsk @Mer__edith
Right, why is this data persistent at all?
Will Dormann
wdormann@infosec.exchange@Mer__edith
From a worse place on the interwebs.
Implying:
Signal message content being present in Apple Notifications database even after Signal itself is deleted is apparently expected and fine.
Signal message content being present for self-deleting messages is not (in their minds).
🤔
Awkward Turing
AwkwardTuring@infosec.exchange@wdormann that's exactly what I was worried about. It suggests that whatever the/an app sends to the notification service gets stored, since OS notification settings would most likely apply only after and not before storage. That's .. creepy but not too surprising.
Thanks for raising awareness!
Will Dormann
wdormann@infosec.exchange@AwkwardTuring
It's easy to fix. It's just somewhat surprising to me that Signal ships with obviously insecure defaults.
Awkward Turing
AwkwardTuring@infosec.exchange@wdormann it is. I'm only worried about all the apps (or users for that matter) that rely on OS' built-in notification settings instead of more granular in-app-settings.
Again: not too surprising but leaves a sour taste nonetheless.
Fritz Adalis
FritzAdalis@infosec.exchange@wdormann @Mer__edith
My expectation as a user would be that the os stores notifications until they're read, unless I make a change otherwise. It seems like they're stored 'forever'.
Will Dormann
wdormann@infosec.exchange@FritzAdalis @Mer__edith
Right. And especially given the black box nature of the iOS platform, it would be nice for some official statements from the Apple and/or Signal side of things.
Nobody wants to be surprised by things like this.
Will Dormann
wdormann@infosec.exchange@Mer__edith
Note the precise use of deleted messages here. When you uninstall the Signal app, that doesn't flag it's messages as "deleted" so that Apple can remove them from the notifications database. (If Apple would ever comply with Signal's demands. iOS (and macOS) don't have such a feature)
I don't think that this behavior maps up with users' expectations of the software. And for Signal to ship knowingly with a default setting that violates user expectations for a secure messaging app, well, I don't like it.
Don't get me wrong, I love the Signal product, and I've donated financially to it multiple times. But this ain't right.
buherator
buheratorI'd compare the persistent (not self-deleting) messages dilemma to secure deletion: below the next architectural boundary you can't really decide what's happening to your data ("were the bits of that file really deleted from the disk?"), but in special cases you take extra steps to prevent leaks ("let's overwrite a bunch of times, hopefully it helps").
@Mer__edith
Will Dormann
wdormann@infosec.exchangeA path that would make me feel more comfortable would be:
We've changed the default setting in Signal to not put message bodies in the (external-to-Signal) notifications database. At least until the dust has settled.
But no, the battle that is being chosen is:
We are pleading with Apple to have self-deleting messages not be permanently retained in the notifications database.
I get that security vs. usability are usually at odds with each other. But I suppose I'd like a bit more transparency here.
buherator
buherator@Mer__edith
Will Dormann
wdormann@infosec.exchange@buherator @Mer__edith
Signal has 100% control of this.
The screenshot is from the Signal iOS app settings.
Signal can't play the "We can't do anything about this" card. It's their default setting that is less secure than it should be.
Alesandro Ortiz 🇵🇷🏳️🌈
AlesandroOrtiz@infosec.exchange@wdormann @Mer__edith FWIW, at least some Android flavors have Notification History feature too. e.g. my Samsung phones have had it for years.
In UI it only shows 24 hours of history and doesn't show uninstalled apps, but not sure if older or uninstalled app notifications are actually deleted behind the scenes.
I agree Signal should have No Content by default. Also needs clear warning about risks when relaxing settings.
Alesandro Ortiz 🇵🇷🏳️🌈
AlesandroOrtiz@infosec.exchange@wdormann Now I'm wondering how Windows behaves here too. Can't test now but IIRC it does store notifs for at least a few days.